What is Rubrik, How It Works, and What It Does for IT Leaders
Rubrik is a data security platform built around the premise that your backup infrastructure is a ransomware target. This guide covers how it works, what enterprise recovery actually looks like, the RPO and RTO benchmarks you can expect, and whether it fits your environment.

What Is Rubrik?
Rubrik is a data security platform that protects enterprise data across on-premises, cloud, and SaaS environments from a single control plane.
It sits in the cyber resilience and data protection category and is built around one core principle: your backup infrastructure is a ransomware target, and it needs to be architected accordingly.
The distinction from traditional backup matters. Legacy backup tools store copies of data. Rubrik treats the backup layer itself as a security boundary, with immutability, access controls, and threat detection built into the architecture rather than bolted on top.
In practice, Rubrik:
- Sits between your production data and your recovery operations
- Captures incremental snapshots and writes them to an immutable file system that cannot be modified or deleted by any external process
- Monitors backup data continuously for indicators of compromise and identifies the last known clean recovery point
- Orchestrates recovery to the original environment, an alternate location, or a cloud clean room
- Manages backup policy, compliance reporting, and anomaly detection through a SaaS control plane that is separated from the on-premises data layer
It's used by mid-to-large enterprises with ransomware recovery SLAs, regulatory compliance obligations, or hybrid and multi-cloud environments where managing separate backup tools for each infrastructure layer has become operationally unsustainable.
How Does Rubrik Work?
At a high level, Rubrik replaces the "backup job" model with a policy-driven data security fabric built around an immutable file system called Atlas.
Instead of scheduling full and incremental backup jobs against individual workloads, you assign SLA policies to workload categories and Rubrik handles capture, storage, replication, anomaly detection, and recovery orchestration from a single control plane.
1. Data Ingestion and Snapshot Capture
Rubrik connects to workloads using:
- Agentless connectors for VMware vSphere and Microsoft Hyper-V
- Lightweight agents for physical servers and NAS
- Native APIs for cloud workloads (AWS EC2, Azure VMs, GCP instances)
- Direct connectors for Microsoft 365, Salesforce, and other SaaS platforms
All workloads assigned to an SLA policy are snapshotted on the defined schedule. Rubrik uses an incremental-forever model. The first snapshot is a full capture; every subsequent snapshot captures only changed blocks.
There are no weekly full backups, no synthetic fulls, and no backup windows to schedule around.
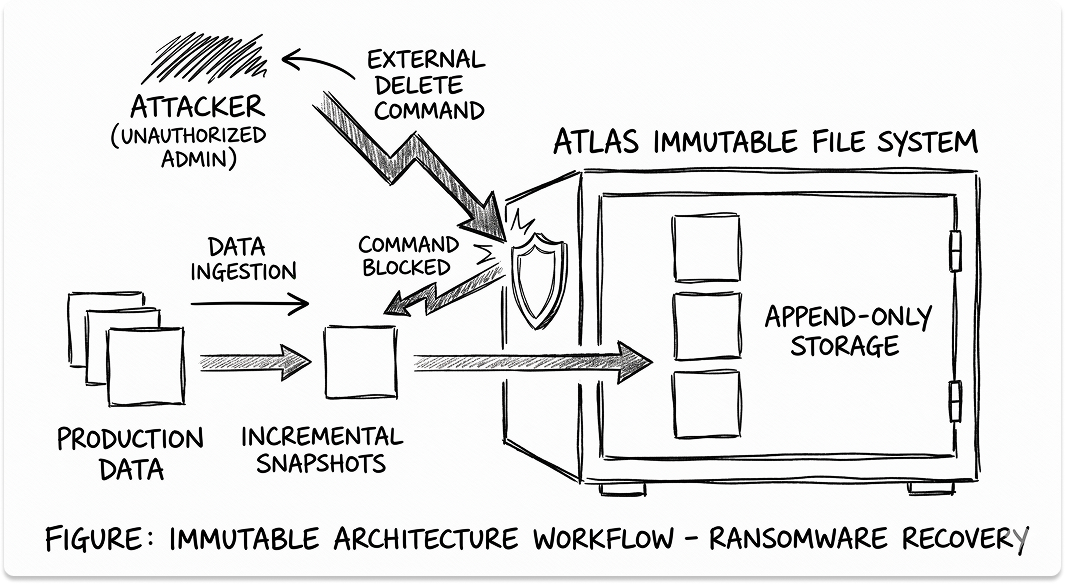
2. The Atlas File System: Why Immutability Is Architectural, Not a Setting
Atlas is Rubrik's distributed file system, and understanding it is the most important part of evaluating the platform.
Data written to Atlas is append-only. There is no mechanism to overwrite or delete a snapshot through an OS-level command, an admin credential, or any external process.
The only way to expire a snapshot is through Rubrik's own policy engine, which requires authenticated, role-separated approval within the platform itself.
This is what makes the claim "ransomware can't encrypt your backups" technically accurate rather than a marketing position.
An attacker who gains domain admin credentials on your production environment has no pathway to modify or delete data in Atlas. The backup layer is structurally isolated from the credential model of the environment it's protecting.
3. The Rubrik Security Cloud Control Plane
Rubrik's management layer runs as SaaS. Policy configuration, anomaly detection, compliance reporting, and recovery orchestration all happen through Rubrik Security Cloud (RSC), which is separated from the on-premises data plane by design.
The practical implication: even if an attacker fully compromises the on-premises environment, they cannot reach the control plane from within it. RSC is not hosted in the data center. There is no on-premises management server to target.

4. Threat Monitoring and Anomaly Detection
Rubrik continuously analyses the backup stream for indicators of compromise: file entropy changes, mass deletion patterns, unusual access behaviour across workloads. This surfaces ransomware activity not by watching live network traffic, but by watching what is changing in the data over time.
When file entropy spikes across a workload's snapshot history, Rubrik flags the anomaly, identifies the affected workloads, and surfaces the last snapshot that preceded the entropy change.
For a security team trying to answer "when did this start and what's recoverable," that's a materially different starting position than manually comparing backup logs.
5. Recovery Orchestration
Recovery in Rubrik is policy-driven and operates at multiple granularities:
- File and folder recovery: Seconds, directly from the snapshot without staging a full restore
- VM recovery via Live Mount: The VM boots directly from the backup snapshot in under five minutes, without waiting for data to be transferred back to production storage
- Application recovery: Pre-staged recovery plans define the sequence, dependencies, and target environment for full application stacks
- Cloud clean room recovery: Rubrik orchestrates recovery into an isolated AWS, Azure, or GCP environment with no connection to the compromised on-premises infrastructure
The difference between a 2-hour RTO and an 8-hour RTO in a ransomware event is almost entirely a function of how much of this was pre-planned and automated before the incident occurred.
Rubrik's Product Architecture: CDM, RSC, and Cloud Vault
Rubrik is not a single product. It is a set of distinct components, each handling a different layer of the data protection architecture. Most evaluation conversations collapse all of them into "Rubrik" without clarifying what is actually being purchased and deployed.
Rubrik Cloud Data Management (CDM): The On-Premises Data Plane
What it does: CDM is the physical or virtual appliance deployed in the data center. It runs the Atlas file system, stores snapshots locally, executes the SLA policies assigned to on-premises workloads, and handles local recovery operations.
Problems it replaces:
- Legacy backup servers with full/incremental job schedules
- Separate deduplication appliances
- Backup infrastructure that shares the same credential model as production
When you need it: Any organisation protecting on-premises workloads: VMware, Hyper-V, physical servers, NAS, Oracle, SQL Server. CDM is the starting point for most enterprise Rubrik deployments.
Key capabilities:
- Incremental-forever snapshots with global deduplication and compression
- Instant recovery via Live Mount for VMware and Hyper-V
- SLA policy-based automation with no manual job scheduling
- Immutable Atlas file system with no external delete pathway
- Local replication to a second CDM cluster for site redundancy
Rubrik Security Cloud (RSC): The SaaS Control Plane
What it does: RSC is the management layer for the entire Rubrik environment. Policy configuration, anomaly detection, threat hunting, compliance reporting, and recovery orchestration all run through RSC, giving a unified view across CDM clusters, cloud workloads, and SaaS environments.
Problems it replaces:
- On-premises backup management servers that are themselves a target in a ransomware attack
- Disconnected management consoles for on-premises and cloud workloads
- Manual compliance reporting processes for backup SLA adherence
When you need it: RSC is included with all Rubrik deployments. It becomes particularly important at scale, when you're managing multiple CDM clusters, cloud workloads, and SaaS protection from a single pane, and when separation of the control plane from the data plane is a specific security or compliance requirement.
Key capabilities:
- Unified policy management across on-premises, cloud, and SaaS
- Ransomware investigation and anomaly detection across the backup stream
- Sensitive data discovery: identifies where PII, PHI, and PCI data exists in backup copies
- Audit-ready compliance reports on SLA adherence, data access, and policy coverage
- Role-based access controls that separate backup administration from production administration
Rubrik Cloud Vault: The Air-Gapped Offsite Copy
What it does: Cloud Vault stores an immutable, logically air-gapped copy of backup data in Rubrik's own cloud infrastructure. There is no persistent network connection between the on-premises environment and Cloud Vault. Data is pushed on a schedule and the connection is closed.
An attacker who controls the on-premises network cannot reach Cloud Vault through that environment.
Problems it replaces:
- Tape offsite rotation (slower, manual, not instantly recoverable)
- Cloud replication targets that share the same access credentials as on-premises backup
- "3-2-1" backup strategies where the offsite copy is reachable from the primary environment
When you need it: Any organisation that needs a guaranteed clean recovery point that survives a full on-premises compromise. Cloud Vault is increasingly required by cyber insurance underwriters as a condition of coverage, and it is the recovery option of last resort in a worst-case ransomware scenario.
Key capabilities:
- Logically air-gapped with no persistent inbound connection from on-premises
- Immutable storage in Rubrik-managed cloud infrastructure
- Recoverable directly to on-premises or to a cloud environment
- Meets the "immutable offsite copy" requirement in most cyber insurance frameworks

Rubrik for SaaS: Microsoft 365, Salesforce, and Google Workspace
What it does: Extends Rubrik's immutable backup and recovery capabilities to SaaS applications. Backs up Exchange Online, SharePoint, OneDrive, Teams, and Salesforce data with the same policy framework and granular recovery options as on-premises workloads.
Problems it replaces:
- The assumption that Microsoft or Salesforce is responsible for protecting your data. Both operate under a shared responsibility model where data protection is the customer's obligation.
- Third-party SaaS backup tools that operate outside the Rubrik policy framework
When you need it: Any organisation using Microsoft 365 or Salesforce at scale where accidental deletion, ransomware, or a rogue admin action would create a material recovery problem.
Most organisations start with CDM for on-premises workloads, connect RSC immediately, add Cloud Vault when cyber insurance or compliance requires an air-gapped copy, and extend to SaaS protection when M365 backup becomes a specific gap.
What Rubrik Offers IT Leaders
Rubrik covers a lot of ground. For IT leaders evaluating it, the capabilities worth understanding map across four areas:
- Ransomware recovery
- Enterprise backup and RPO/RTO
- Data compliance and governance
- Multi-cloud and SaaS data protection
Ransomware Recovery
IT leaders don't fear ransomware in the abstract. They fear the specific moment when someone asks "can we recover?" and the honest answer is "we don't know." Rubrik's ransomware recovery capabilities are built to make that answer knowable before the incident, not during it.
1. Why Your Backup Infrastructure Is the Primary Target
Veeam's 2024 Ransomware Trends Report found that in 93% of ransomware attacks, attackers specifically targeted backup repositories before triggering encryption. If the backups are destroyed or encrypted alongside production data, the victim has no recovery path and is far more likely to pay.
Traditional backup tools store data in formats and locations that are reachable from the same credential model as production.
An attacker with domain admin access can delete backup jobs, corrupt repositories, or encrypt backup storage the same way they encrypt everything else. Rubrik's Atlas file system removes that pathway structurally. There is no OS-level or credential-based mechanism to modify or delete snapshot data.
For a broader view of how ransomware is reshaping security architecture decisions, the Stryker cyberattack analysis covers what the pattern of a real enterprise breach looks like and what it means for recovery planning.
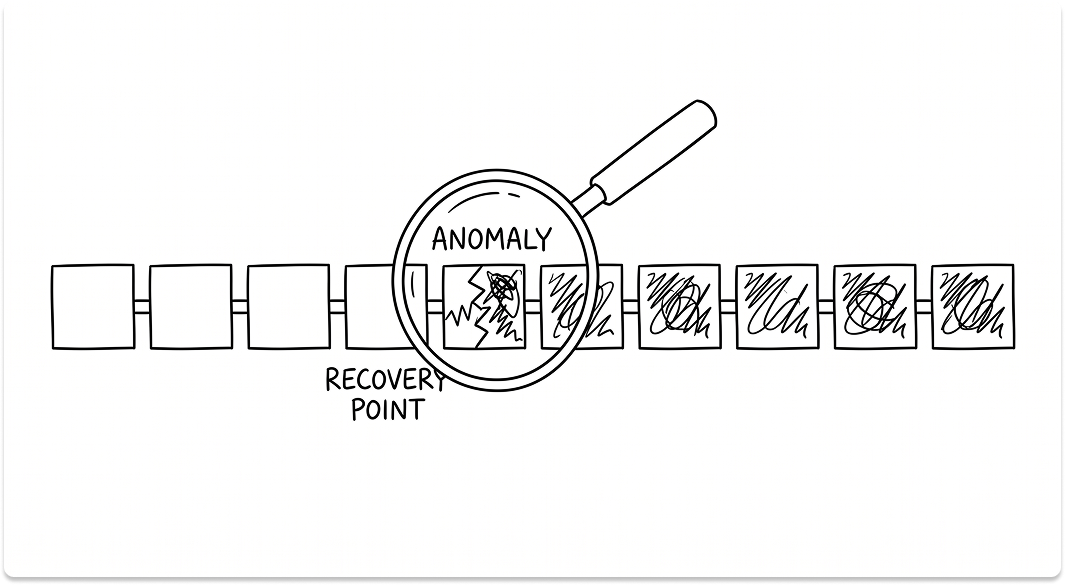
2. The Clean Recovery Point Problem
The hardest operational question in a ransomware response is not "can we restore?" It's "restore to when?" Ransomware often has a dormancy period of 14 to 45 days between initial compromise and encryption trigger.
Backups taken during that window may contain infected files, corrupted data, or attacker-planted persistence mechanisms. Restoring to a snapshot from three days ago may reintroduce the problem.
Rubrik's anomaly detection monitors the backup stream for the point at which file behaviour changed: entropy spikes, mass deletions, unusual modification patterns.
It surfaces the last snapshot that preceded the anomaly as the recommended clean recovery point. For a security team under active incident response, that's the difference between a defensible recovery decision and a guess.
3. Recovery Time in a Ransomware Event
Rubrik supports three recovery models relevant to ransomware response:
- Live Mount for immediate VM availability: the VM boots directly from the backup snapshot in under five minutes, without waiting for data to be moved back to production storage. This is how you keep critical systems running while the full recovery proceeds.
- Bulk recovery with orchestration: pre-staged recovery plans define the sequence and dependencies for recovering full application stacks. The plan runs automatically rather than being executed manually by an incident response team under pressure.
- Cloud clean room recovery: Rubrik orchestrates recovery into an isolated cloud environment with no connection to the compromised on-premises infrastructure. This is used when the production environment is too compromised to recover into safely, or when forensic investigation needs to proceed in parallel.
For a practical guide on what enterprise ransomware recovery actually looks like end to end, how do you fight ransomware when there's nothing left to restore covers the recovery sequence in detail.
Enterprise Backup and RPO/RTO
1. What the Incremental-Forever Model Means for RPO
Traditional backup architectures run a weekly full backup with daily incrementals, which puts RPO at 24 hours for most workloads and introduces backup windows that affect production performance.
Rubrik's incremental-forever model takes frequent snapshots, as often as every 15 minutes for critical workloads, without the storage overhead of repeated full backups.
For environments with tight RPO requirements in financial services, healthcare, or manufacturing, this changes what's achievable without a proportional increase in storage cost.
2. SLA Policy Management at Scale
Rubrik manages backup frequency, retention, replication, and archival through SLA policies rather than per-workload job configuration. You define an SLA, hourly snapshots, 30-day local retention, replicate to Cloud Vault after 7 days, and assign it to a workload category.
Every workload in that category is handled automatically. No job scheduling, no manual monitoring of individual backup tasks, no exceptions that fall through because someone forgot to configure a new VM.
For teams managing hundreds or thousands of workloads, this is operationally significant. The alternative, per-workload job configuration in a traditional backup tool, doesn't scale, and the gaps it creates are exactly what ransomware operators look for.
3. RPO and RTO Benchmarks in Practice
Rubrik supports RPOs as low as 15 minutes for VMware and Hyper-V workloads. RTO for a single VM via Live Mount is under five minutes.
For full application recovery, RTO depends on the recovery plan configuration and the target environment, but pre-staged recovery plans consistently reduce recovery time by a factor of three to five compared to manual restore processes.
For a full comparison of how Rubrik's RPO and RTO benchmarks stack up against Veeam, Cohesity, and Commvault, the enterprise backup software RPO/RTO comparison covers those metrics across the major platforms.
The top data backup and recovery solutions guide is also worth reading if you're still mapping the broader vendor field before narrowing to a shortlist.
Data Compliance and Governance
1. Sensitive Data Discovery in Backup Copies
Most organisations can tell you where regulated data lives in production. Very few can tell you where it lives in their backup copies. Rubrik scans backup data for sensitive data classifications, PII, PHI, PCI-DSS, and surfaces where regulated data exists across the environment, including in snapshots retained beyond their intended lifecycle.
For compliance teams under GDPR right-to-erasure obligations or HIPAA data minimisation requirements, this answers a question that is otherwise extremely difficult to address systematically.
2. Audit-Ready Compliance Reporting
RSC generates reports on backup coverage, SLA adherence, data access, and policy exceptions. For organisations under SOC 2, HIPAA, or ISO 27001 obligations, this reduces the manual effort of demonstrating that data protection controls are operating as designed.
The reports are formatted for auditor consumption, not raw log exports that require interpretation.
3. Separation of Duties on the Backup Layer
Rubrik's role-based access controls enforce separation between production administration and backup administration. The administrator who manages your VMware environment cannot also manage or delete backup data.
This separation is a specific control requirement in SOC 2 and is increasingly required by cyber insurers as a condition of coverage, particularly for organisations that have experienced a prior incident.
For a practical framework on how data protection obligations factor into vendor selection and compliance planning, what tech vendors must know about data protection concerns covers the regulatory and contractual dimensions in detail.
Multi-Cloud and SaaS Data Protection
1. The Coverage Gap Most Teams Discover After an Incident
Most enterprise backup strategies were designed for on-premises infrastructure. When workloads move to AWS, Azure, or GCP, and when teams adopt Microsoft 365 and Salesforce, those environments frequently fall outside the existing backup architecture, not because anyone decided to leave them unprotected, but because the backup tool in place simply didn't cover them.
Rubrik extends the same SLA policy framework, immutability guarantees, and recovery orchestration to cloud workloads and SaaS applications without requiring a separate tool for each environment.
For organisations navigating a cloud migration that's brought new backup gaps with it, the AWS Migration Hub vs Azure Migrate vs Google Cloud comparison covers how the major cloud migration platforms handle data protection handoffs.
2. Cloud-Native Workload Protection
Rubrik protects AWS EC2 instances, RDS databases, Azure VMs, and GCP workloads natively through RSC. Policy assignment, anomaly detection, and recovery orchestration work the same way as on-premises workloads.
A cloud VM assigned to an SLA policy is backed up, monitored, and recoverable through the same interface as a VMware VM in the data center, which matters operationally when an incident spans both environments.
3. SaaS Data Is Not the Vendor's Responsibility
Microsoft's shared responsibility model explicitly states that Microsoft 365 data protection is the customer's responsibility.
Microsoft provides platform availability and replication within their infrastructure, but accidental deletion, ransomware targeting M365 data, and rogue admin actions are recovery scenarios the customer owns.
Rubrik for Microsoft 365 backs up Exchange Online, SharePoint, OneDrive, and Teams with the same immutability and granular recovery capabilities as on-premises workloads. Individual emails, files, and Teams conversations are recoverable in seconds.
See Which Rubrik Component Best Suits Your Needs
Answer the questionnaire below and we'll give you recommendation for getting started with the right Rubrik component.
Is Rubrik Right for Your Environment?
Rubrik is a strong fit for some environments and worth evaluating carefully in others.
Rubrik is likely the right conversation if:
- You've had a ransomware incident or near-miss and recovery capability is now a board-level or cyber insurance requirement
- Your current backup tool doesn't give you a defensible answer on "what's the last clean recovery point" after an encryption event
- You're managing backup across on-premises, cloud, and SaaS and running separate tools for each
- You have RPO/RTO SLAs in contracts, compliance frameworks, or service agreements that your current architecture cannot reliably demonstrate
- Cyber insurance renewal is coming up and underwriters are asking about backup immutability, air-gapped copies, or separation of duties on backup administration
- Your backup infrastructure shares the same credential model as production, meaning a compromised admin account could reach backup data
Evaluate carefully or consider alternatives if:
- Your environment is predominantly small-scale or single-site, backup complexity is low, and existing tools are meeting SLA requirements without gaps
- Your primary workloads are already in a cloud environment with mature native backup services and the gap you're solving is narrow
- You have limited IT operational capacity for initial deployment. Rubrik's SLA model materially reduces ongoing operational work, but the initial deployment and policy configuration requires structured effort and planning time
For a structured view of how Rubrik compares to Veeam and Cohesity across RPO, RTO, ransomware protection, and licensing models, the Rubrik vs Cohesity vs Veeam comparison guide covers those dimensions in detail.
If you're still working through the broader vendor selection process, the IT vendor selection criteria and checklist and the vendor due diligence best practices guide are useful frameworks before any shortlist conversation.
Evaluating data protection or cyber resilience vendors?
Tell us your requirements over a meeting and we will send a shortlist of vendors worth your time. If you want to take things forward, we'll prep the vendors before the call so your conversation starts from context.
FAQ
What is Rubrik used for?
Rubrik is used to protect enterprise data from ransomware, manage backup and recovery across on-premises and cloud environments, meet RPO and RTO SLAs, and demonstrate data protection compliance to auditors and cyber insurers. It's deployed by organisations that need immutable backups, fast recovery from ransomware events, and a single management layer across hybrid infrastructure.
What is Rubrik backup?
Rubrik backup is an incremental-forever snapshot model that captures changed data blocks on a defined schedule and stores them in an immutable file system called Atlas. Snapshots cannot be modified or deleted by any external process, including OS-level commands or compromised admin credentials. Backup frequency, retention, and replication are managed through SLA policies rather than individual job configuration.
How does Rubrik work?
Rubrik connects to workloads through agentless connectors, agents, or native cloud APIs, captures incremental snapshots on the schedule defined in the assigned SLA policy, and writes them to the Atlas file system on a CDM appliance or cloud storage. The Rubrik Security Cloud control plane manages policy, monitors for anomalies in the backup stream, and orchestrates recovery. Because the control plane is SaaS-based and separated from the on-premises data layer, it remains accessible and intact even if the on-premises environment is compromised.
What is Rubrik enterprise recovery?
Rubrik enterprise recovery refers to the platform's ability to orchestrate recovery of full application stacks across on-premises and cloud environments. Recovery plans define the sequence, dependencies, and target environment for workload recovery and can be executed automatically. For ransomware events, this includes Live Mount for immediate VM availability, bulk recovery with pre-staged orchestration, and clean room recovery into an isolated cloud environment.
How does Rubrik protect against ransomware?
Rubrik's ransomware protection operates at the architecture level. The Atlas file system is append-only: there is no mechanism for ransomware or a compromised admin credential to modify or delete snapshot data. Rubrik Security Cloud monitors the backup stream for anomalies including file entropy changes, mass deletions, and unusual modification patterns, and identifies the last known clean recovery point before the anomaly occurred. Cloud Vault provides a logically air-gapped offsite copy that survives a full on-premises compromise.
What is Rubrik Security Cloud?
Rubrik Security Cloud (RSC) is the SaaS-based control plane for the Rubrik platform. It provides unified policy management, anomaly detection, sensitive data discovery, compliance reporting, and recovery orchestration across all connected CDM clusters, cloud workloads, and SaaS environments. Because RSC is hosted outside the on-premises environment, it remains accessible during an on-premises incident and cannot be reached or compromised through the production network.
What is Rubrik Cloud Vault?
Rubrik Cloud Vault is an immutable, logically air-gapped copy of backup data stored in Rubrik's own cloud infrastructure. There is no persistent network connection between the on-premises environment and Cloud Vault. Data is pushed on a defined schedule and the connection is closed. It is the recovery option of last resort in a full on-premises compromise and is increasingly required by cyber insurance underwriters as a condition of coverage.
How does Rubrik compare to Veeam?
Rubrik and Veeam address the same problem from different architectural starting points. Veeam is a backup and replication platform with a broad ecosystem of integrations and a per-workload job model. Rubrik is a data security platform with an immutable file system, SLA-based policy management, and an integrated ransomware detection layer. For organisations where ransomware resilience and backup immutability are the primary evaluation criteria, Rubrik's architecture provides structural guarantees that Veeam requires additional configuration and third-party tooling to approximate. The Rubrik vs Cohesity vs Veeam comparison guide covers the differences across RPO, RTO, and cyber resilience capabilities in detail.
What RPO and RTO can Rubrik achieve?
Rubrik supports RPOs as low as 15 minutes for VMware and Hyper-V workloads through its incremental-forever snapshot model. RTO for a single VM via Live Mount is under five minutes. Full application stack recovery time depends on the recovery plan configuration and target environment, but pre-staged orchestration consistently reduces RTO by a factor of three to five compared to manual restore processes. The enterprise backup software RPO/RTO comparison benchmarks these figures against Veeam, Cohesity, and Commvault.
Is Rubrik a SaaS platform?
Rubrik has a SaaS component, Rubrik Security Cloud, which serves as the control plane for policy management, monitoring, and recovery orchestration. The data plane, where backup data is stored, can be on-premises via CDM appliances, in cloud storage, or in Rubrik Cloud Vault. Most enterprise deployments are hybrid: CDM on-premises for local workloads, RSC in the cloud for management, and Cloud Vault for the air-gapped offsite copy.