The Stryker Cyberattack: What This Means for Your Security Architecture
Iran-linked group Handala wiped 200,000+ Stryker devices using Microsoft Intune, not malware. Full technical breakdown and what IT leaders need to fix before the same attack hits them.

On March 11, 2026, employees at Stryker offices across dozens of countries turned on their computers and found them wiped. Login screens displayed the logo of Handala, an Iran-linked hacktivist group.
Stryker confirmed "a global network disruption to our Microsoft environment as a result of a cyber attack," noting it had no indication of ransomware or malware and believed the incident was contained.
Stryker is a Fortune 500 company that specializes in surgical equipment, orthopedic implants, and neurotechnology. Headquartered in Michigan, the company employs approximately 56,000 people and reported over $25 billion in revenue for 2025. Its critical role in the healthcare supply chain makes it an essential partner for hospitals worldwide.
The attack's technical mechanism is the detail that matters most for every infrastructure and security leader reading this. It was not a novel zero-day. It was not custom malware that evaded every layer of detection. It was Stryker's own endpoint management platform, turned against itself.
The Attack Mechanism: Microsoft Intune as the Weapon
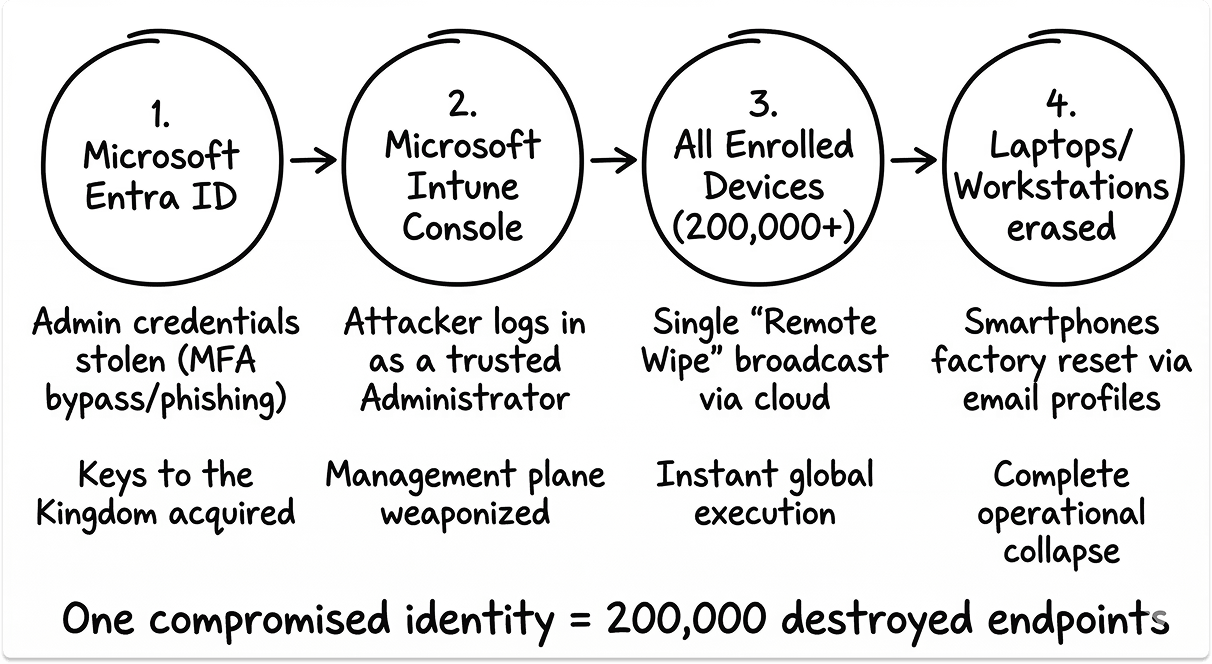
The attackers compromised administrator accounts and weaponized Microsoft Intune, Stryker's cloud-based mobile device management platform, to issue remote wipe commands to all connected devices. This is a "living off the land" technique that turned Stryker's own IT management infrastructure against itself.
Intune is a cloud-based MDM solution that gives IT teams a single administrative console to manage, configure, and wipe devices globally, regardless of where those devices sit.
When an attacker gains admin-level access to that console, they inherit the same capabilities. Every enrolled endpoint becomes reachable with a single command.
The reconstructed attack sequence points to: credential compromise, where attackers gained access to privileged administrator accounts within Stryker's Microsoft Entra ID environment through likely credential harvesting, MFA bypass, or supply-chain compromise of an IT service provider, followed by MDM weaponization, where using compromised admin credentials, attackers accessed the Microsoft Intune console and issued enterprise-wide remote wipe commands.
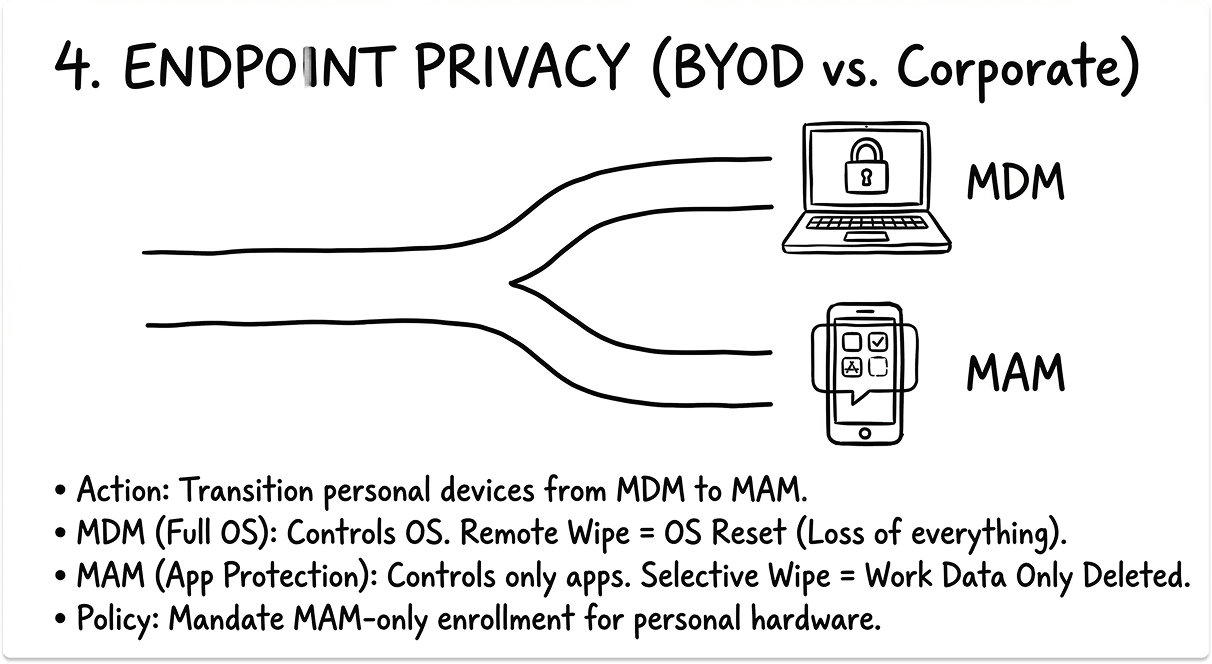
Employees reported that anything connected to the network was down, and that anyone with Microsoft Outlook on their personal phones had their devices wiped.
Staff enrolled their personal devices for corporate email or Teams access, meaning those devices were enrolled in the same MDM profile as corporate assets, and subject to the same remote wipe command.
Unit 42's 2026 Global Incident Response Report notes that 65% of initial access in recent incidents is driven by identity-based techniques enabling unauthorized access, privilege escalation, and lateral movement.
What happened at Stryker is consistent with that pattern. The attacker did not need to compromise 200,000 machines individually. They needed one credential set with sufficient privilege in the right management plane.
Scope and Downstream Impact
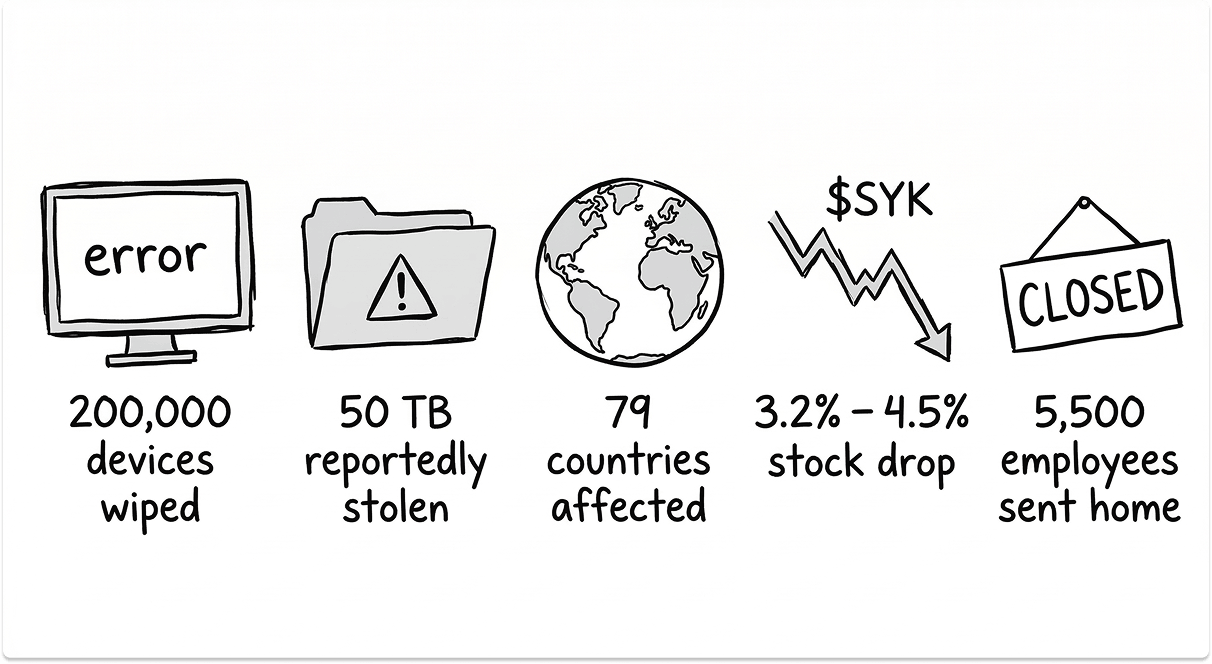
The hackers claim to have wiped more than 200,000 servers, mobile devices, and other systems, forcing Stryker to shut down offices in 79 countries. They also claim to have stolen 50TB of data.
Handala has a documented pattern of inflating breach claims, so both figures should be treated with appropriate skepticism until independent verification is possible. The operational disruption, however, is confirmed.
Reports from Stryker employees in many countries, including the U.S., Ireland, and Australia, confirmed devices were remotely wiped overnight. In Ireland, Stryker's largest hub outside the United States, approximately 5,500 employees were sent home as internal networks went offline. Numerous employees reported that the attack forced some locations to revert to pen and paper workflows after systems became unavailable.
The impact extended to patient care workflows. One piece of Stryker equipment disrupted was Lifenet, an IT system emergency responders use to transmit patient ECG data to hospitals.
Maryland's Institute for Emergency Medical Services Systems notified hospitals that Stryker's Lifenet electrocardiogram transmission system was non-functional across most of the state. When prehospital ECG data cannot reach the receiving hospital before an ambulance arrives, preparation time for time-sensitive cardiac conditions shrinks.
Stryker's stock was down approximately 3.2% in Wednesday afternoon trading following the attack. The company subsequently filed an 8-K disclosure with the SEC. Handala also claims to have exfiltrated data from Stryker before executing the wipe, though the extent of any impact on device firmware, medical device data, or electronic protected health information is not yet confirmed.
Who Handala Is and Why Stryker Was Targeted
Palo Alto Networks links Handala to Iran's Ministry of Intelligence and Security. Palo Alto says Handala surfaced in late 2023 and is assessed as one of several online personas maintained by Void Manticore, a MOIS-affiliated actor.
According to IBM X-Force, Handala employs a broad and evolving toolkit, including phishing, custom wiper malware, ransomware-style extortion, data theft, and hack-and-leak activity.
Its campaigns consistently feature ideological messaging, inflated or misleading breach claims, and deliberate targeting of life-critical sectors such as healthcare and energy.
Stryker was chosen for specific reasons. The Handala manifesto referred to Stryker as a "Zionist-rooted corporation," which may be a reference to the company's 2019 acquisition of the Israeli company OrthoSpace.
The company also holds a $450 million contract to supply medical devices to the U.S. Department of Defense. The Stryker attack is the first confirmed major cyberattack on a U.S. corporation since joint U.S.-Israeli military strikes on Iran began on February 28, 2026.
A report from the Center for Strategic and International Studies found that Iran has historically relied on cyber operations and that the February 28 strikes were more likely to mark the beginning of a new phase of cyber escalation than its conclusion.
Palo Alto researchers described recent Handala activities as opportunistic and "quick and dirty," with a noticeable focus on supply-chain footholds through IT and service providers to reach downstream victims, followed by proof posts to amplify credibility and intimidate targets.
That supply-chain vector is worth holding onto. It surfaces again when you look at how the initial access likely occurred.
The Prior Breach and What It Reveals About Detection
Stryker had a prior 2024 breach involving unauthorized access for approximately one month from May to June 2024, with personally identifiable information including medical records exfiltrated. That breach was not disclosed until December 2024.
A six-month gap between breach discovery and public disclosure raises questions about detection capability and incident response maturity that go beyond the March 2026 attack.
Under HIPAA, covered entities and business associates have 60 days from discovery to notify affected individuals of a breach. Whether that threshold was met is a separate regulatory question, but the timeline of that earlier incident provides context for understanding the current one.
It is not yet confirmed whether Handala established fresh administrative access in the weeks before March 11, or whether persistence from the 2024 compromise, or a related foothold, remained in the environment.
The Handala branding that appeared on screens before the wipe confirms that access had been established and held well before the destructive phase began. This was a deliberate, staged operation.
The pattern is consistent across major wiper attacks: initial access, quiet reconnaissance and privilege escalation, then a single destructive action executed from a high-privilege position. The dwell time before the destructive phase is where defenders have the best chance of intervention.
If that window is not being monitored adequately, the first signal of compromise is a blank screen.
Where Your Vendor and MSP Relationships Introduce Risk
The Securonix incident reconstruction notes supply-chain compromise of an IT service provider as one of the likely initial access vectors. This deserves attention, because it is a structural issue the Stryker incident makes visible.
Palo Alto has specifically noted Handala's focus on supply-chain footholds through IT and service providers to reach downstream victims. When your MDM platform, your SIEM, your endpoint detection tool, or your identity management system is administered partially or fully by a third-party provider, that provider's credential posture becomes part of your attack surface.
I have seen this pattern repeatedly. An organization invests in a strong internal security program, enforces phishing-resistant MFA on internal accounts, and builds solid privileged access management. Then an MSP or managed security services provider has a standing service account in the environment with persistent admin rights, protected by a password and an SMS-based MFA code. The MSSP's security posture is weaker than the client's own posture. The attacker targets the path of least resistance.

The questions you need to answer about every vendor with admin access to your environment:
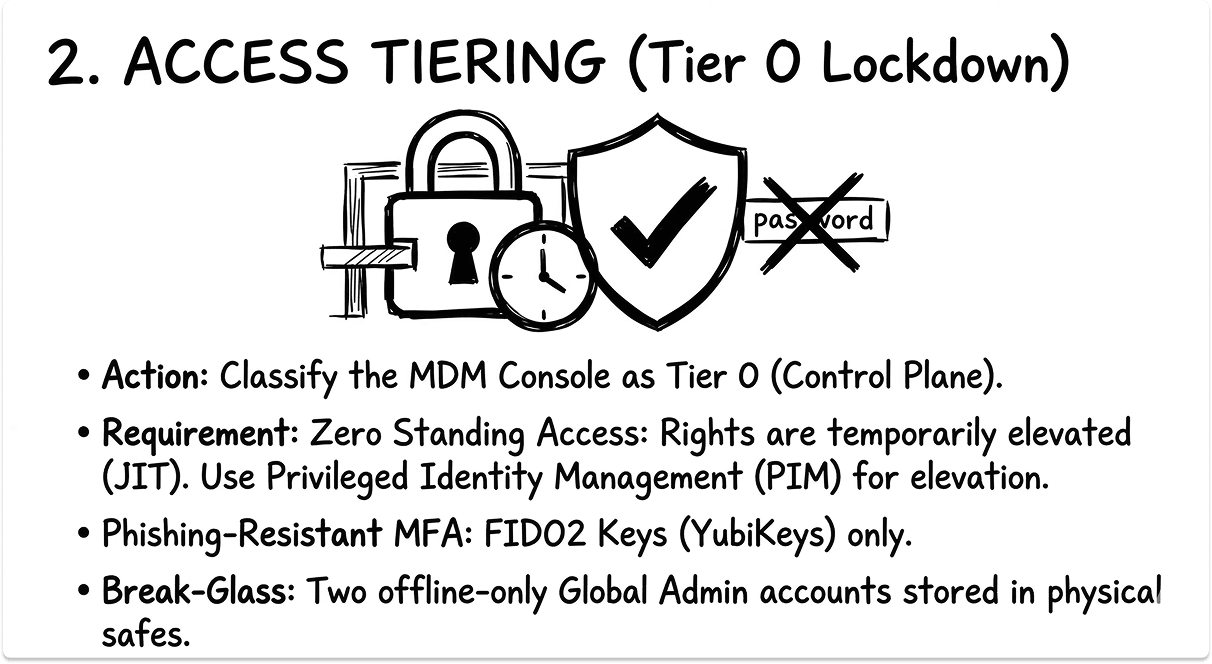
- What MFA type protects their access to your systems? SMS and TOTP are insufficient for Tier 0 platforms. Phishing-resistant MFA, FIDO2 hardware keys or passkeys, is the minimum for any account that can issue a global device wipe.
- Do they have persistent admin access, or is access granted just-in-time and revoked after the session?
- What conditional access policies govern their access? Are there alerts for anomalous access patterns, like an admin account operating outside business hours or initiating bulk actions against large device sets?
- What does your contract require of them in terms of security controls, incident notification timelines, and breach liability? Most MSP contracts are thin on this.
- When did you last audit their access? Not review a report they provided. Actually audit: pull the sign-in logs, check what accounts have been active, verify that former employees of the MSP no longer hold service accounts in your environment.
The third-party access problem has a long track record. The 2020 SolarWinds attack moved through the software supply chain. Numerous subsequent breaches have moved through MSP and IT service provider footholds.
The operational pattern described as "quick and dirty" with supply-chain footholds suggests initial access could have been established days or weeks prior, with the destructive payload executed rapidly once the right privilege level was reached.
Vendor access reviews need to be a standing operational process, not an annual checkbox on a compliance audit.
The MDM Architecture Problem Your Security Team Needs to Solve
The Stryker incident makes concrete a risk that most organizations have acknowledged abstractly but not addressed architecturally: your MDM admin console is your single most dangerous management plane.
Intune, Jamf, SCCM, and equivalent platforms exist because centralized endpoint management is operationally necessary at scale. A small IT team cannot manually configure thousands of endpoints.
But the same centralized control that makes MDM operationally efficient creates a single point of catastrophic failure when the admin credentials are compromised.
Separate your MDM admin identity from your standard identity. The admin account used to manage Intune should not be the same account used to receive email, attend Teams meetings, or browse the web. If your Intune global admin reads phishing emails on the same account that has device wipe authority, a single successful phish can result in a mass wipe event.

Treat MDM admin access as Tier 0. In Microsoft's Active Directory tiering model, Tier 0 assets are those that can control the entire identity and endpoint infrastructure. Your MDM console qualifies. Apply the same access controls: no persistent privileged sessions, dedicated admin accounts separate from daily-use accounts, all admin actions logged and alerted on, and break-glass accounts stored offline with access procedures documented separately from systems that could be wiped.
Build anomaly detection around high-risk MDM actions. A legitimate IT administrator does not typically initiate a remote wipe on 200,000 devices at 3 a.m. That action, at that scale, at that hour, should trigger an automatic alert and a hold requiring secondary approval. Most organizations have not built this logic into their MDM workflows because the tooling supports it but no one has configured it.

Revisit BYOD enrollment policies. If personal devices are enrolled with full MDM management profiles rather than containerized Mobile Application Management profiles, those devices are subject to a corporate remote wipe command. Employees were unable to log into accounts because they had used their phones to provide two-factor authentication codes and lost all personal data from enrolled personal devices. MAM-only enrollment can wipe corporate app data without touching personal data. That is the appropriate policy for personal devices in most environments.
Offline Recovery Readiness
Numerous employees reported the attack forced some locations to revert to pen and paper workflows. In some organizations, that transition is a total failure mode. In others, it is a pre-planned fallback that keeps critical operations running at reduced capacity.
The difference is whether someone has written and tested the offline runbook. Most organizations have disaster recovery plans for infrastructure failures. Fewer have documented manual operating procedures for the scenario where every network-connected device is simultaneously unavailable for a week.
Recovery from a wiper attack is measured in weeks to months. Each wiped endpoint needs a clean image rebuild, MDM re-enrollment, re-authentication, and application re-provisioning.
At scale across multiple geographies, that is a logistics operation as much as a technical one. Organizations that do not maintain offline system inventories, backup images on isolated storage, and manual provisioning procedures will discover those gaps during recovery, not before it.
The Regulatory and Institutional Gap
As of March 11, 2026, no U.S. government agency had issued a specific advisory, alert, or official statement about the Stryker attack. CISA is operating at approximately 38% staffing due to a federal funding lapse.
The agency tasked with coordinating sector-wide cyber defense for critical infrastructure was absent from the immediate response to one of the largest cyberattacks on a U.S. healthcare company in recent memory.
The CSIS assessment that Iran's February 28 strikes were more likely to mark the beginning of a new phase of cyber escalation than its conclusion makes the capacity gap at CISA a material operational risk for organizations in healthcare, defense supply chains, and critical infrastructure.
Organizations in those sectors cannot treat government response as a reliable primary layer of cyber resilience right now. Sector-sharing groups like the Health Information Sharing and Analysis Center (H-ISAC) and the Healthcare and Public Health Sector Coordinating Council exist precisely for this scenario: peer intelligence-sharing when federal response capacity is constrained.
The Architecture Takeaway
Iran's destructive cyber capability is not new. The 2012 Shamoon attack erased data from more than 30,000 systems at Saudi Aramco. What has changed is the delivery method. Shamoon required malware deployment and execution on individual systems. The Stryker attack, if the Intune vector is confirmed, required a browser, an admin credential, and a single action in a cloud console.
The shift from deploying wiper malware to abusing legitimate cloud management tools mirrors a broader pattern in how attackers operate: use what the environment already has, minimize detectable artifacts, and execute at maximum scale. Your threat model needs to account for this, and your MDM, identity management, and third-party access governance are where that work starts.
The CEO of Smartech247, commenting on Handala's current activity, said: "Any organisation has to be on very, very significant high alert to potentially be hit by these guys because they're quite sophisticated, they have a lot of resources. And their sole objective is chaos."
When the objective is disruption rather than financial gain, the attack economics change. There is no negotiation phase, no opportunity to restore systems by paying a ransom. The only variable is how prepared your organization is to detect the compromise before the destructive action executes, and how quickly you can recover when it does.
Also read: What NotPetya's Attack on Maersk Tells us About Legacy System Risks
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
Was the Stryker attack ransomware?
No. Stryker confirmed there was no ransomware or malware. It was a wiper attack, executed through Stryker's own Microsoft Intune platform after admin credentials were compromised. The goal was destruction, not extortion.
Who is Handala?
Handala is an Iran-linked hacktivist group assessed by Palo Alto Networks as a persona operated by Void Manticore, a threat actor tied to Iran's Ministry of Intelligence and Security. They target critical infrastructure for ideological reasons, not financial gain.
Is Stryker medical equipment safe to use?
Stryker says Lifenet is functioning and customer communications are normal. However, several hospitals are independently assessing whether to disconnect Stryker-connected equipment from their own networks while the investigation is ongoing. Verify with your account rep and internal security team.
How did attackers get in?
Not publicly confirmed. The most credible reconstruction points to a compromised high-privilege Entra ID admin account, through phishing, MFA bypass, or a third-party IT provider. Stryker also had an undisclosed breach in mid-2024, raising unresolved questions about prior persistence.
What should other organizations do right now?
Audit every account with MDM global admin rights. Enforce phishing-resistant MFA on those accounts. Review whether your MSP holds persistent admin access and whether their credential hygiene matches your own standards. This attack required no novel exploit, only a compromised admin credential and an unsecured management console.




