What is Zscaler, How it Works, and What it Does for IT Leaders
Discover what Zscaler is, how it works, which architecture best suits you, and what it offers IT leaders in cyberthreat protection, data security, IoT/mobile, and Zero Trust for branch & cloud.
What Is Zscaler?
Zscaler is a cloud-native security platform that delivers protection and access control from the cloud instead of through traditional on‑premises firewalls and VPNs. It sits in the Security Service Edge (SSE) category and is built around Zero Trust principles: no user, device, or app is trusted by default—every request is verified and evaluated in real time.
In practice, Zscaler:
- Sits between your users/devices and the internet, SaaS, and internal apps
- Authenticates identity and inspects traffic in the cloud
- Applies security and data policies inline
- Connects users and workloads only to the specific applications they’re allowed to reach—never to your entire network
It’s used heavily by mid‑ to large‑scale organizations with distributed workforces, significant SaaS and cloud adoption, and strong security or compliance pressure.
How Does Zscaler Work?
At a high level, Zscaler replaces the “data center as the hub” model with a cloud security fabric called the Zero Trust Exchange. Instead of dragging traffic back to your network, you send it to Zscaler’s globally distributed cloud, where security and access decisions are made.
1. Traffic onboarding
You onboard traffic to Zscaler using:
- A lightweight endpoint agent
- Proxy/PAC settings
- Tunnels from branches or data centers (e.g., SD‑WAN / router integration)
All relevant traffic (internet, SaaS, private app) is steered to the nearest Zscaler data center.
2. Identity and context verification
Zscaler integrates with your identity provider (Azure AD, Okta, Ping, etc.) to check:
- Who the user is (identity, groups, role)
- What device they’re on (managed/unmanaged, OS posture)
- Where they are (location, network)
- When and how they’re accessing (time, behavior patterns, risk signals)
Every connection is evaluated per session, not just at first login.
3. Policy decision
Based on your policies, Zscaler decides, for each request:
- Allow, block, or require step‑up authentication
- Apply specific controls (e.g., DLP, read‑only, watermarking)
- Route via the appropriate path (internet/SaaS vs. private app)
Policies consider identity, device, app, content, and context, not just IP/port.
4. Inline inspection
Zscaler acts as a full proxy:
- Decrypts SSL/TLS where allowed
- Inspects traffic with multiple engines:
- URL/category filtering
- Malware detection and sandboxing
- Command‑and‑control and phishing detection
- DLP and data classification
- Re‑encrypts and forwards traffic
All of this happens inline in the cloud, close to the user and the destination app.
5. Application‑specific connection
For internet/SaaS:
- Zscaler forwards clean, policy‑compliant traffic to the destination service.
For private apps (ZPA):
- Connectors you deploy inside your environment make inside‑out connections to Zscaler.
- Apps are not exposed on the internet (no inbound ports, no VPN gateways).
- Zscaler brokers a connection from the validated user to the specific app—without ever putting the user “on the network.”
Result: users never gain broad IP‑level reach into your environment; they only gain access to the apps they’re allowed to use.
Zscaler Product Architecture: ZIA, ZPA, and ZDX
Zscaler is not a single product. It is three distinct modules, each solving a different problem, each licensed separately. Most evaluation conversations collapse all three into "Zscaler" without clarifying which module is actually being discussed.
Zscaler Internet Access (ZIA)
What it does: Secures all outbound internet and SaaS traffic. This is the core product. Every user request to a website, SaaS application, or cloud service routes through ZIA, where it is inspected for threats, DLP violations, and policy compliance before reaching its destination.
Problems it replaces:
- On-premises internet firewalls and secure web gateways
- Legacy proxy appliances
- MPLS backhaul of branch traffic to a central data center for inspection
When you need it: Any organization with distributed users, heavy SaaS adoption, or compliance requirements around data leaving the network. ZIA is typically the first Zscaler product deployed.
Key capabilities in ZIA:
- SSL/TLS inspection at scale
- URL and content filtering
- Cloud sandboxing for unknown file execution
- Inline DLP across web and SaaS channels
- CASB for shadow IT discovery and SaaS posture management
- Firewall-as-a-service for non-web traffic
Zscaler Private Access (ZPA)
What it does: Replaces VPN for access to internal applications. Users connect to specific private applications — hosted on-premises, in AWS, Azure, or GCP — without ever being placed on the corporate network. The application is never exposed to the internet. Zscaler brokers the connection between the user and the app, invisibly.
Problems it replaces:
- VPN concentrators and remote access infrastructure
- Network-level access that grants more connectivity than the user needs
- Lateral movement risk from over-permissioned remote access
When you need it: Organizations replacing VPN, securing third-party or contractor access, or migrating internal applications to private cloud environments. ZPA is frequently the trigger for a Zscaler evaluation when a VPN contract is coming up for renewal.
Key capabilities in ZPA:
- Application-level access with zero network exposure
- Continuous identity and device posture verification per session
- Works across on-premises data centers, AWS, Azure, GCP, and partner environments
- App connectors deploy inside the environment with no inbound firewall rules required
- Supports browser-based access for unmanaged devices without an agent
Zscaler Digital Experience (ZDX)
What it does: Monitors end-to-end user experience from the device to the application. ZDX continuously measures the performance of every hop in the connection path, including the Zscaler cloud, the ISP, and the application itself, and correlates degradations with specific segments of the path.
Problems it replaces:
- Blind troubleshooting of "the internet is slow" complaints
- Reactive IT support for remote user performance issues
- Disconnected monitoring tools that see network performance but not application delivery quality
When you need it: Organizations that have deployed ZIA or ZPA and need visibility into whether Zscaler or something else in the path is causing performance issues. ZDX is typically the third product deployed, after ZIA and ZPA are established.
Key capabilities in ZDX:
- Real-time performance scoring per user, per application
- Path tracing from endpoint through ISP, Zscaler node, and application
- Proactive alerting before users raise support tickets
- Integrates with ITSM tools for automated ticket creation on degradation events
Most organizations start with ZIA, add ZPA when VPN renewal comes up, and add ZDX once the user base is large enough that reactive troubleshooting becomes operationally expensive.
What Zscaler Offers to IT Leaders
Zscaler is broad; for IT leaders, it’s helpful to look at what it offers through four lenses:
- Cyberthreat protection
- Data security
- IoT & mobile security
- Zero Trust for branch and cloud
Cyberthreat Protection
IT leaders are constantly balancing innovation against the fear of a breach that defines their career. Zscaler’s cyberthreat protection is designed to reduce that fear in practical ways.

1. Reduce attack surface
- App invisibility: Internal applications aren’t exposed on the public internet; no open inbound ports, no published VPN gateways.
- No network access: Users never join your network; they get brokered, app‑specific connectivity.
- Microsegmentation by design: Lateral movement is dramatically harder because there’s no flat, reachable network from the user’s perspective.
This directly cuts down the avenues for recon, scanning, and lateral movement.
2. Inline threat prevention at cloud scale
Because Zscaler sits inline for user traffic, it can:
- Inspect encrypted traffic without overloading on‑prem appliances
- Block malware, ransomware, phishing, and exploit attempts before they reach users
- Use global threat intelligence (from hundreds of billions of daily transactions) to recognize patterns your local stack might miss
Threat prevention is always on, for:
- Office users
- Remote/hybrid workers
- Branch locations
- Users on untrusted networks
3. Stronger incident detection and response
Zscaler’s logs and analytics help your SOC:
- See web/SaaS/private app activity from a single viewpoint
- Correlate user behavior, threat events, and DLP violations
- Use integrations with SIEM/XDR to enrich investigations
That shortens the “What actually happened?” phase and supports faster, more confident response.
Data Security
Most IT leaders are held personally accountable not just for keeping systems up, but for keeping data in. Zscaler’s data security capabilities are built to enforce your policies wherever data flows.
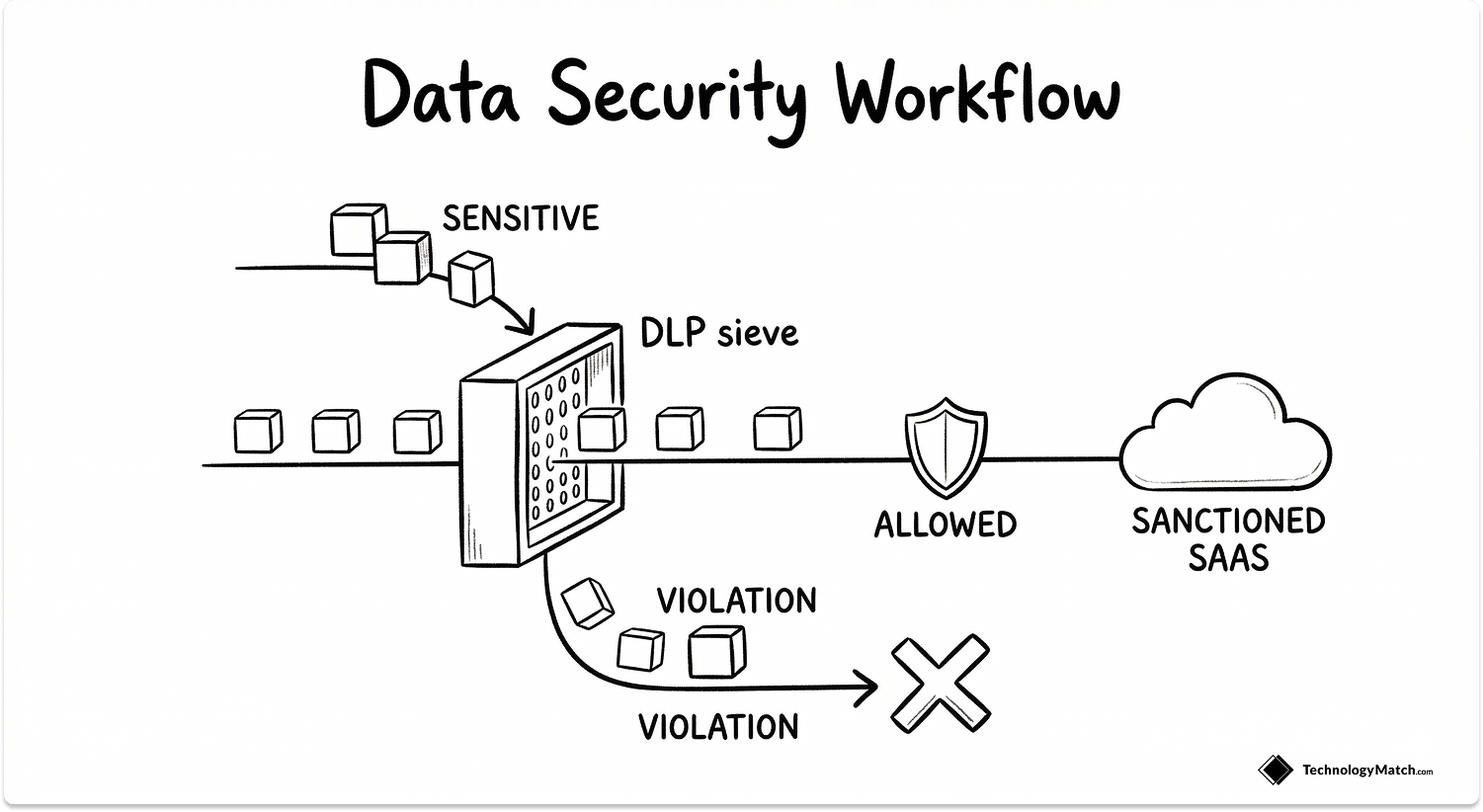
1. inline DLP across channels
Zscaler can inspect:
- Web traffic (uploads, posts, forms)
- SaaS traffic (file shares, chat, collaboration)
- Private application access
- Email (via integration)
and apply DLP policies in real time, such as:
- Blocking uploads of regulated data (PII, PHI, PCI)
- Preventing copy/paste into unsanctioned destinations
- Warning and coaching users on risky behavior
- Allowing but logging certain flows for audit
2. SaaS and cloud data posture
Through CASB and SaaS security posture controls, Zscaler helps you:
- Discover which SaaS apps are actually in use (sanctioned and shadow IT)
- Classify apps by risk and enforce access policies accordingly
- Check for misconfigurations that could expose data externally
- Apply consistent controls across multiple SaaS providers
3. Compliance‑aligned controls and reporting
Zscaler’s data protection features support common compliance needs by:
- Providing detailed logs of access, violations, and policy actions
- Enforcing location‑ and content‑based restrictions (e.g., EU data residency)
- Supporting reports suitable for auditors and regulators
This shifts you from “we hope our policies are followed” to “we can show how they’re enforced and monitored.”
IoT & Mobile Security

Your risk is no longer just laptops on corporate LANs. You’re dealing with:
- Mobile users on Wi‑Fi you don’t control
- Devices that aren’t full PCs (tablets, phones, scanners, rugged devices)
- IoT/OT systems that often lack modern security controls
Zscaler extends Zero Trust concepts into this territory.
1. Securing mobile users everywhere
With the Zscaler client on mobile devices:
- User traffic is steered to Zscaler regardless of network (home Wi‑Fi, hotel, cellular).
- The same security stack—SWG, CASB, DLP, threat prevention—is applied.
- Policies are user/identity‑centric, not tied to IP or physical location.
This means your mobile workforce gets:
- Consistent protection
- Consistent access experience
- Reduced need for separate mobile gateways/VPN logic
2. Visibility and control for “unmanaged” edges
For devices you can’t or don’t fully manage (e.g., some BYOD, contractor devices, or thin IoT/OT telemetry endpoints), Zscaler can help via:
- Network‑level steering (e.g., via SD‑WAN, router, or Wi‑Fi controller)
- Policy based on source network/zone, app, and content
- Central visibility into which devices/segments are communicating where
This doesn’t magically fix insecure IoT/OT design, but it gives you control points and visibility you’d otherwise lack.
3. IoT/OT access to cloud and internal apps
For IoT/OT devices that need:
- Access to cloud APIs or services
- Access to internal dashboards or control systems
Zero Trust principles mean you can:
- Limit each device or segment to only the minimum necessary destinations
- Apply inline inspection where feasible
- Monitor and log all communications for anomaly detection
Compared to “flat VLAN and ACL” approaches, this is a step toward constrained, observable access for inherently risky device classes.
Zero Trust for Branch and Cloud
For many IT leaders, the biggest structural headache is aligning branches and cloud with a Zero Trust model.
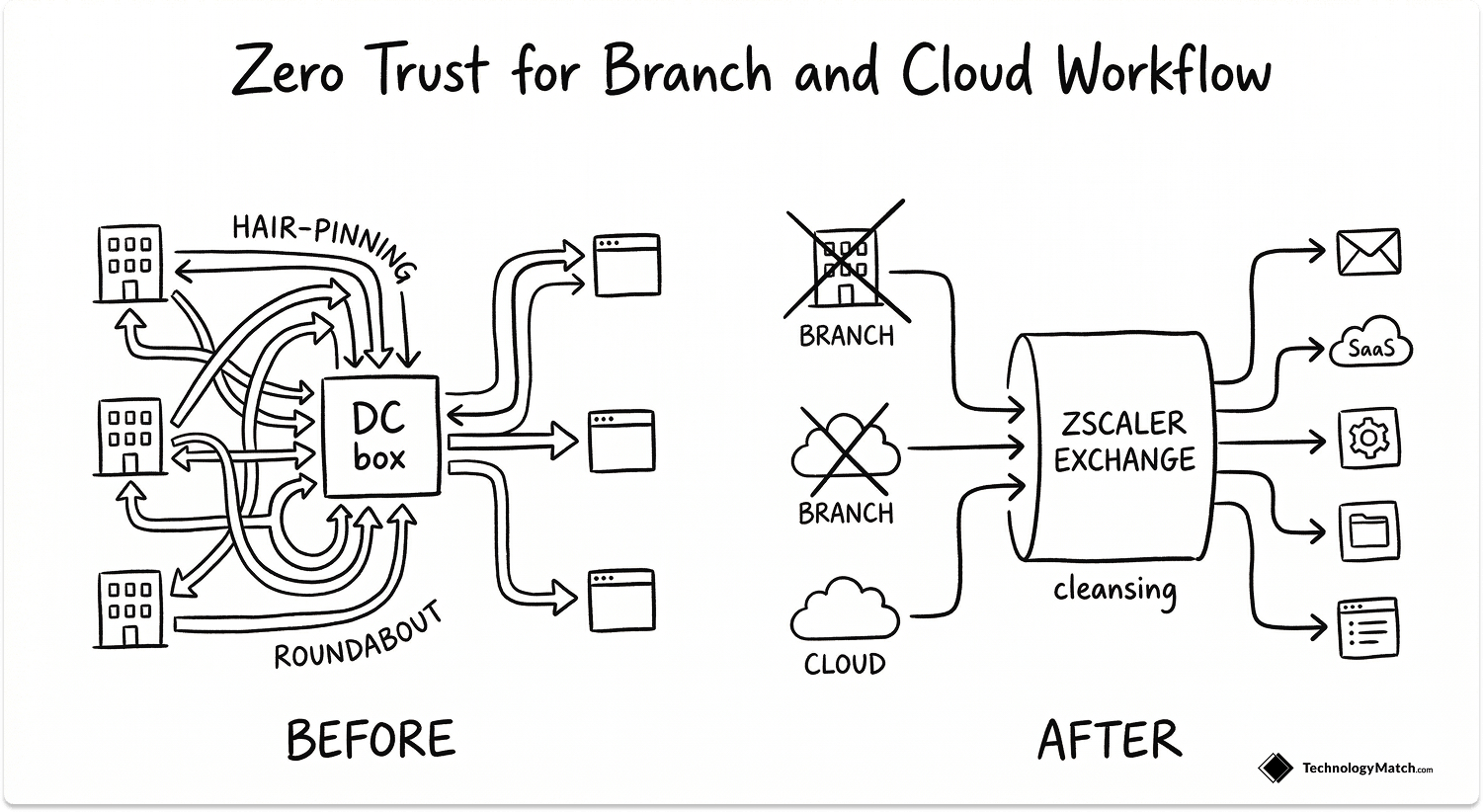
1. Branch transformation
Traditional branch model:
- MPLS or VPN backhaul to data center
- Local or centralized firewalls
- Complex routing and underlay/overlay management
With Zscaler in the mix:
- Branches can use local internet breakouts; traffic is sent to Zscaler instead of your DC.
- You can often reduce or eliminate MPLS for internet/SaaS access.
- Security stack (SWG/CASB/DLP/Threat Protection) is now cloud‑delivered.
Benefits:
- Lower WAN costs (depending on MPLS footprint)
- Better SaaS performance (no hairpinning)
- Uniform security across branches and remote users
2. Zero Trust access to internal apps (ZPA)
Instead of standing up VPN gateways in each DC/region:
- You deploy Zscaler connectors in your data centers or VPCs.
- Apps are published via ZPA, not exposed to the internet or tied to IP ranges.
- Users authenticate to Zscaler and get app‑specific connections.
This works across:
- On‑prem data centers
- Private clouds (AWS, Azure, GCP)
- Partner‑hosted environments
Result: a logical, application‑centric fabric over your hybrid/multi‑cloud footprint without having to tightly mesh all your networks for user access.
3. Multi‑cloud connectivity and workload‑to‑workload
Beyond user access, Zscaler can also support workload‑to‑workload connectivity:
- Microservices in one cloud securely talk to back‑end systems in another
- Policies govern which services can talk to which others (again: app‑centric, not IP‑centric)
- Inspection and logging apply to inter‑service traffic where configured
This helps you progress from:
“Cloud 1 talks to Cloud 2 over a big IP tunnel we hope is locked down”
toward:
“Service A is allowed to talk only to Service B on defined paths, controlled and logged.”
For an IT leader trying to put structure around accelerating cloud sprawl, that’s not trivial.
Read more: How does Zscaler compare to Netskope, Palo Alto, and Cato while choosing an SASE tool.
See Which Zscaler Architecture and Offering Best Suits Your Needs
Answer the questionnaire below and we'll give you recommendation for getting started with the right Zscaler architecture and offering.
Is Zscaler Right for Your Environment?
Zscaler fits organizations that have accepted that the perimeter is gone. Users are distributed, applications are in the cloud, and the traditional model of routing everything through a central data center for inspection is a performance and security liability.
If that describes your environment, Zscaler is worth a serious evaluation. Start with ZIA if internet and SaaS security is the priority. Start with ZPA if VPN replacement is the trigger. Add ZDX when the user base is large enough that reactive troubleshooting is costing your team time.
If you are still running the majority of your workloads on-premises with a largely office-based workforce, the operational overhead of Zscaler may outweigh the benefit at this stage. The architecture is built for distribution. The more distributed your environment, the stronger the case.
The evaluation question is not whether Zscaler is a good product. It is whether your infrastructure has moved far enough away from the perimeter model to make cloud-delivered security enforcement the right architectural decision for the next five years.
Also read: IT Leaders' Guide to Choosing a Managed Kubernetes Service
We can help you find SASE vendors
If you're evaluating Zscaler, or trying to figure out whether it's the right fit over other alternatives, that's exactly the kind of call we set up. Tell us your environment and priorities. We'll match you with the vendors worth talking to.
FAQ
What does Zscaler do?
Zscaler is a cloud-native security platform that sits between your users and the internet, SaaS applications, and internal systems. Every connection is authenticated, inspected for threats and policy violations, and routed to its destination — without the user ever touching the corporate network. It replaces on-premises firewalls, VPN concentrators, and web proxies with a cloud-delivered security layer that follows the user regardless of location.
Is Zscaler a VPN?
No. A VPN places the user on the corporate network, granting broad access to everything on that network segment. Zscaler gives users access to specific applications only — the network itself is never exposed. This removes the lateral movement risk that makes compromised VPN credentials dangerous. ZPA, Zscaler's private access module, is the VPN replacement. It connects users to apps, not networks.
Is Zscaler a firewall or a proxy?
Neither in the traditional sense. A firewall inspects traffic at the network perimeter based on IP and port. A traditional proxy sits inside your network and inspects outbound web traffic for a fixed user population. Zscaler is a full inline proxy delivered from the cloud, inspecting all traffic including encrypted SSL/TLS sessions, for every user on any network. It belongs to the Security Service Edge (SSE) category — security enforcement in the cloud, not at a perimeter.
What is the Zscaler Client Connector?
The Zscaler Client Connector is the lightweight agent installed on managed endpoints that steers all device traffic to the nearest Zscaler data center for inspection. It replaces the VPN client and runs silently in the background. For unmanaged devices or contractor access, Zscaler also supports browser-based access via ZPA without requiring the agent to be installed.
How does Zscaler integrate with existing tools?
Zscaler integrates with identity providers (Microsoft Entra ID, Okta, Ping Identity) for user authentication, EDR platforms (CrowdStrike, Microsoft Defender) for device posture signals, SIEMs (Splunk, QRadar, Microsoft Sentinel) for log forwarding, and SD-WAN vendors (Cisco, VMware, Palo Alto) for branch traffic steering. All integrations are pre-built. No custom development is required.





