A Vendor Risk Assessment Guide For IT Leaders in 2026
A complete guide to vendor risk assessment for IT leaders: how to tier vendors, score risk domains, handle AI and fourth-party exposure, meet DORA requirements, and turn findings into enforceable contract terms.

Vendor risk assessment is the structured process of identifying, measuring, and mitigating the risks a vendor introduces before you sign a contract and throughout the life of the relationship.
In IT, it means evaluating a vendor's security posture, operational resilience, financial stability, compliance standing, and AI governance practices before their failure becomes your incident.
Done well, vendor risk assessment does three things simultaneously: it forces evidence in place of claims, it creates contractual leverage while you still have alternatives, and it produces the documentation regulators now explicitly require.
Why vendor risk assessment matters more in IT than anywhere else
Every IT vendor relationship is a data flow, an integration, and a trust relationship. Each one extends your attack surface. When a vendor is breached, misconfigured, or goes under, the damage lands in your environment, on your users, and in your audit log.

The numbers bear this out. According to the Verizon 2025 Data Breach Investigations Report, third-party involvement in data breaches doubled to 30% of all incidents, up from roughly 15% the year before.
The SecurityScorecard 2025 Global Third-Party Breach Report found 35.5% of breaches are now linked to third-party access. Research compiled by Secureframe puts the share of organizations that experienced at least one supply chain breach in 2025 at 97%.
Most IT vendor programs were not built for this environment. They were built for a world of fewer vendors, longer contracts, and more predictable risk profiles. The shift to SaaS, cloud, and AI-embedded tooling has changed all three. A program that was adequate three years ago is a liability today.
The 2026 vendor risk landscape: four threats your assessment must cover
Third-party breach risk. Supply chain attacks have become a preferred attacker strategy because compromising one trusted vendor provides access to dozens of downstream organizations simultaneously. Smaller vendors are disproportionately targeted as an easier vector into larger, better-defended enterprises. The CDK Global ransomware attack took down roughly 15,000 car dealerships through a single vendor. This is the model attackers are replicating.
AI vendor risk. According to Accorian's research on AI risk in third-party vendor tools, 78% of organizations now use third-party AI tools, with more than half relying exclusively on them rather than building in-house. This creates a category of risk that standard security questionnaires were not designed to capture. SOC 2 reports have no controls for prompt injection, training data provenance, or model hallucination. Per the IBM 2025 Cost of a Data Breach Report, 13% of organizations reported breaches involving AI models or applications, and 97% of those organizations lacked proper AI access controls.
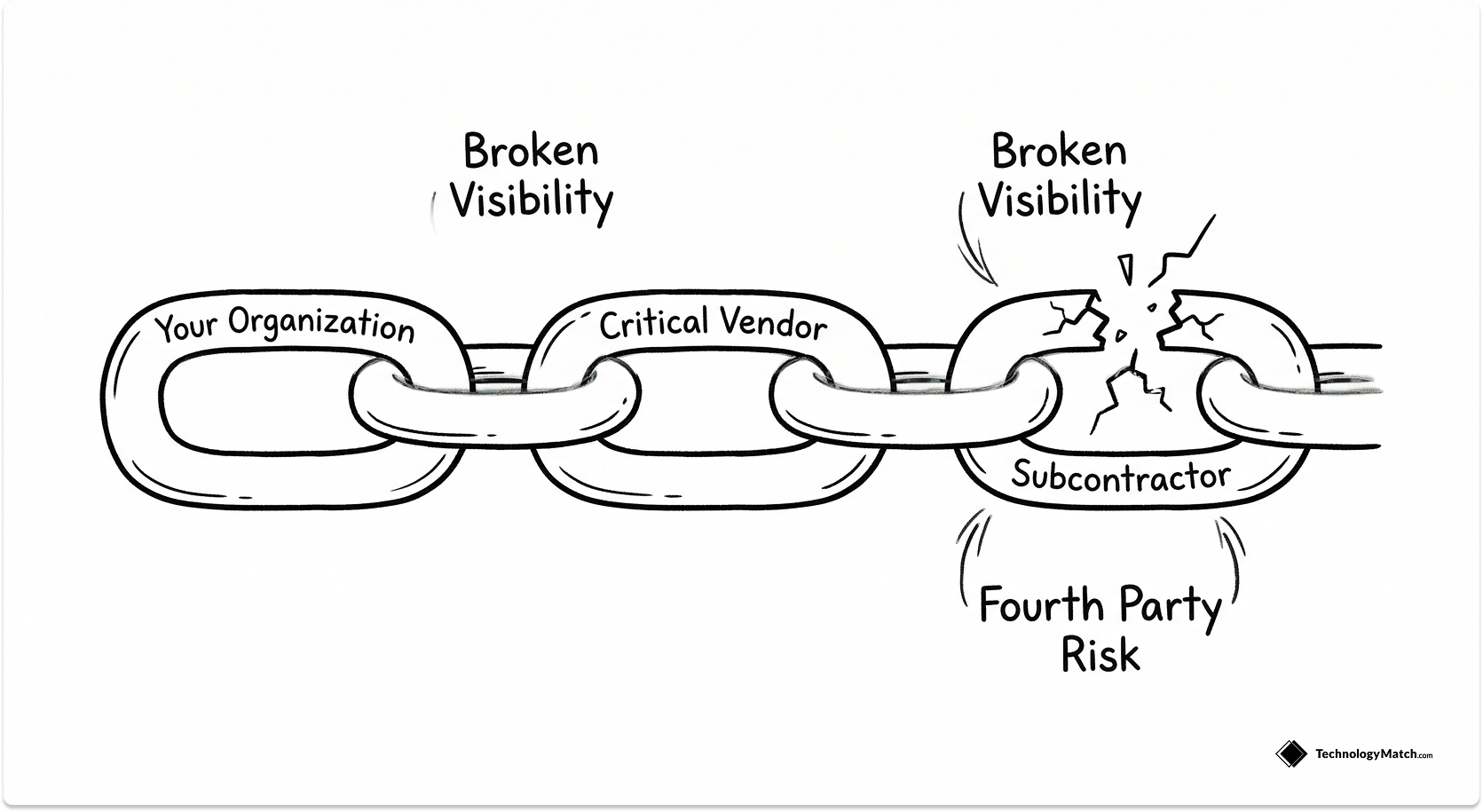
Fourth-party risk. Fourth-party risk is the exposure introduced by your vendors' vendors, the subcontractors and cloud services that sit one step removed from your organization but still touch your data or can cause cascading failures. According to SecurityScorecard, fourth-party breaches account for 4.5% of all breaches, and 12.7% of third-party breaches extend into fourth-party incidents. Only 10% of organizations conduct direct fourth-party risk assessments.
Concentration risk. The 2024 CrowdStrike outage illustrated what happens when too many vendors share a single dependency. A faulty sensor update caused cascading failures not because of cloud provider failure, but because of homogeneous dependency on one endpoint protection vendor. In 2026, this risk extends to AI: organizations deploying the same foundation model across fraud detection, customer service, and credit scoring are creating model monocultures where a single training data vulnerability propagates uniformly across use cases.

Types of vendor risk assessments
Before any questionnaire goes out, define what data the vendor will process, which systems they will touch, what privileges they require, and what your substitution options are. This inherent risk scoping determines assessment depth, reviewer assignment, and decision timelines.
Security and privacy due diligence covers the core of most assessments: SIG/CAIQ questionnaires, SOC 2 Type II or ISO 27001 reports, penetration test results with remediation status, vulnerability management metrics, data processing agreements, and data residency commitments.
Operational resilience reviews examine whether the vendor can maintain or restore services when things go wrong: documented RTO and RPO targets, BCP/DR test results with actual recovery times, and support tier commitments with escalation paths.
Financial viability checks assess vendor survival risk. A technically excellent vendor with three months of runway is a continuity risk you cannot outsource. Request financial statements, insurance certificates, litigation disclosures, and adverse media screening.
Compliance mapping verifies the vendor meets your regulatory obligations across GDPR, CCPA, HIPAA, PCI, and DORA where applicable.
AI-specific assessment must be applied to any vendor deploying AI in their product, not just pure-play AI vendors. This is covered in detail below.
How to conduct a vendor risk assessment: step by step
1. Define inherent risk and tier the vendor
Clarify what data the vendor will process, which systems they will touch, and what privileges they require. Assign a Tier 1 (high risk), Tier 2 (medium), or Tier 3 (low) rating based on data sensitivity, access level, business impact, regulatory exposure, and substitutability. This tier determines diligence depth, required reviewers, and decision SLAs.
2. Plan scope and assign owners
Frame the assessment across security, operational resilience, compliance, financial viability, and strategic fit. Assign clear owners before sending anything to the vendor. Procurement manages intake and deadlines. Security evaluates controls. Legal maps residual risks to contract clauses. Architecture validates integration and blast radius. The business owner accepts residual risk.
3. Request a standard evidence pack
Ask for SOC 2 Type II report, recent penetration test with remediation status, BCP/DR plans with actual RTO/RPO test results, data processing agreement, subprocessor list, incident response documentation, financial statements, insurance certificates, and sanctions screening. Require substantive evidence, not attestations.
4. Validate and test claims
Confirm evidence is current, the auditor is independent, and the trust service criteria match your use case. Sample controls with concrete artifacts: access reviews, change tickets, backup restore proofs. Pull external signals from sanctions databases, adverse media, and security ratings tools such as SecurityScorecard or Bitsight.
5. Score risks using a 5-point rubric with weights
Evaluate each risk domain on a 1 to 5 likelihood-by-impact scale, weighted to context. Security and privacy carry higher weight for SaaS processors; financial stability carries more weight for managed service providers. Calculate a weighted composite score and produce a risk heatmap.
6. Define thresholds and decision outcomes before reviewing
Establish decision thresholds before you start: composites at or below 2.0 approve, 2.1 to 3.4 approve with conditions, 3.5 or higher reject or require an executive waiver. Treat certain failures as automatic no-go regardless of composite score, including no encryption at rest for PII, no incident response documentation, and refusal to provide SOC 2.
7. Convert findings into contractual safeguards
Risk findings not in the contract disappear after signing. Use a security and privacy addendum to set control baselines for encryption, identity, logging, and breach notification timelines. Reserve audit rights and assessment refresh obligations. Lock down data residency, return and deletion timelines, and subprocessor change notification requirements.
8. Build a remediation plan you can verify
For every open finding, define the control to implement, the evidence required to prove closure, the acceptance criteria, and a named owner on both sides. Tie deadlines to project milestones or payment gates. Compensating controls are acceptable for findings that cannot be remediated immediately, but they must be documented.
9. Decide in a single executive session
Prepare a one-page decision memo: vendor overview, tier, domain scores, composite, top risks, mitigations, conditions, residual rating, and named owners. Bring Security, Legal, Procurement, Architecture, and the business owner together for a 30 to 45-minute session. Record the outcome, any dissenting views, accepted conditions, and next steps.
10. Hand off to vendor management
Store the full record in a single system of record. Define reassessment cadence by tier: quarterly for Tier 1, annual for Tier 2, attestation-based for Tier 3. Set change-event triggers that automatically initiate reassessment: M&A activity, scope expansion, repeated SLA failures, or material security incidents.
Use the following vendor risk assessment calculator to understand the risk associated with each vendor under consideration:
- Enter vendor details.
- Score the vendor based across 5 (optional 6) primary and essential metrics.
- The calculator gives you a score that you can use as metric to compare vendors in the vendor selection process.
This calculator has been made based on our conversations with thousands of IT leaders across industries and of various sizes and scale.
AI vendor risk assessment: the layer most programs are missing
Standard assessments were designed before AI became embedded in enterprise software. A SaaS tool using an LLM to generate summaries or flag anomalies has risk vectors that no SOC 2 report covers. Prompt injection, data poisoning, model inversion, and model extraction are documented attack patterns with real enterprise consequences, not theoretical risks.
Any vendor deploying AI in a product you use should answer the following questions before you sign:
Training data and data use. Does the vendor use customer data to train or fine-tune their models? The commitment must be in the DPA, not just the acceptable use policy. Acceptable use policies can change unilaterally. Only DPA terms are enforceable.
Model supply chain. What foundation model does the vendor's product use, and who provides it? Require vendors to document their entire AI supply chain, including which third parties have access to your data through the AI layer.
AI-specific attack surface. Ask vendors how they test for prompt injection and adversarial inputs, what their documented methodology is, and when they last ran adversarial testing.
Model output governance. For decisions affecting your business or customers, can the vendor explain, audit, and override AI outputs when something goes wrong? If the vendor cannot answer this, the liability sits with you.
Change notification. AI models change through retraining and version updates. Require contractual notification of material model changes and reassessment rights when they occur.
Regulatory frameworks are catching up. EU AI Act enforcement began in 2025. DORA's third-party ICT risk obligations explicitly include AI-embedded services for financial entities. ISO 42001 Clause 8.4 covers AI supplier relationship requirements.
Fourth-party risk: the exposure most programs never reach
Your vendor's vendors are your problem, even though you have no contract with them. Software supply chain compromises accounted for 75% of third-party breaches in 2025. For every direct vendor in a supply chain, organizations typically have indirect relationships with nearly 14 times more fourth and fifth parties, according to research cited by Secureframe.
Three controls close the most critical gaps:
Require subprocessor disclosure and change notification in contracts. Your vendor should maintain a current subprocessor list, notify you of changes before they occur, and give you a right to object. This is already required under GDPR for data processors. Apply it to all critical vendors regardless of data classification.
Use SOC 2 Type II reports as a window into fourth parties. SOC 2 reports must disclose subservice organizations and the controls they provide. Review the subservice organization section to identify critical fourth parties you did not know existed.
Map concentration risk across your portfolio. Ask how many of your critical vendors rely on the same cloud provider, the same identity platform, or the same AI foundation model. Concentration in fourth-party infrastructure is as dangerous as concentration in direct vendors.
DORA: what it requires and who it affects
If your organization is a financial entity operating in the EU, or an ICT service provider supporting EU financial entities, DORA became enforceable on January 17, 2025. It requires financial entities to maintain a register of all ICT third-party service providers, conduct documented risk assessments before contracting and at least annually thereafter, include contractual provisions covering security requirements, incident reporting, audit rights, and subcontracting chain oversight, and report third-party risk assessments annually to their supervisory authority.
Critically, DORA's subcontracting chain requirements mean you must assess the subcontractors supporting critical or important functions, not just your direct vendors. This is the regulatory codification of fourth-party risk management for financial services. For organizations outside financial services, NIS2 extends similar third-party risk requirements to operators of essential services across a broad range of sectors.
Metrics that prove your program is working

Decision speed: Median days from intake to risk decision by tier. Target under 5 business days for Tier 3, under 15 for Tier 2, under 30 for Tier 1. Rework rate (decisions reopened due to missing evidence) should be below 10%.
Risk shift left: Count P1 and P2 issues found before contract signature versus after go-live. A rising pre-contract ratio means your assessment is capturing real risk when the cost of change is lowest.
Remediation effectiveness: Percentage of conditional approvals closed by their deadline. Target above 85%. Track aging open items and repeat findings per vendor.
Operational outcomes: Vendor-attributed incidents by tier and severity. If Tier 1 vendors generate the same incident rate as Tier 3 vendors, your tiering criteria need recalibration.
Monitoring health: Percentage of Tier 1 and Tier 2 vendors with current evidence within their required refresh cadence. Target above 95%. Evidence staleness is the leading indicator of program decay.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What is vendor risk assessment in IT and how does it impact vendor selection?
Vendor risk assessment evaluates a vendor's security, compliance, operational resilience, financial stability, and AI governance practices before contract signature. It supplies the evidence, scores, and thresholds that drive faster, safer vendor selection decisions and produces the documentation regulators require.
What are the main types of vendor risk assessments?
The primary types are security and privacy due diligence (SIG/CAIQ, SOC 2, ISO 27001, pen tests, DPAs), operational resilience reviews (BCP/DR, RTO/RPO), financial viability checks, compliance mapping (GDPR, HIPAA, PCI, DORA), strategic and technical fit analysis, and AI-specific assessment for vendors deploying AI in their products.
How do you conduct a vendor risk assessment step by step?
Define inherent risk and tier the vendor, plan scope and assign owners, request a standard evidence pack, validate and test claims, score risks using a weighted 5-point rubric, establish thresholds before reviewing, convert findings into contractual safeguards, build a verifiable remediation plan, decide in a single executive session, and hand off to vendor management with a defined reassessment cadence.
What is fourth-party risk and why does it matter?
Fourth-party risk is the exposure created by your vendors' vendors. According to SecurityScorecard, 12.7% of third-party breaches extend into fourth-party incidents, and only 10% of organizations conduct direct fourth-party assessments. Managing it requires subprocessor disclosure clauses, SOC 2 subservice organization reviews, and concentration mapping across your vendor portfolio.
What does DORA require for vendor risk assessment?
DORA, enforceable since January 17, 2025, requires financial entities and ICT service providers in the EU to maintain a vendor register, conduct documented risk assessments before contracting and annually thereafter, include contractual provisions covering security, incident reporting, and subcontracting chain oversight, and report third-party risk assessments annually to their supervisory authority.
How is AI vendor risk different from standard vendor risk assessment?
Standard questionnaires and SOC 2 reports have no controls for AI-specific risks including prompt injection, training data provenance, model hallucination, data poisoning, or model inversion. AI vendor assessment requires additional scrutiny of training data use, foundation model supply chain, adversarial testing methodology, model output governance, and contractual notification rights when models are updated.




