How to Run an IT Vendor Proof of Concept
Most IT vendor POCs test what the vendor wants to demonstrate. This framework gives IT leaders a structured approach to designing, running, and scoring a proof of concept that surfaces real technical gaps before the contract is signed.

A structured IT vendor POC framework for CIOs, CISOs, and Infrastructure Heads. Covers test design, failure scenarios, integration testing, scoring, and how to use POC findings in contract negotiations.
What Is an IT Vendor Proof of Concept?
An IT vendor proof of concept (POC) is a structured technical evaluation where you test a vendor's product in your environment, against your requirements, before signing a contract.
Most POCs test what the vendor wants to demonstrate, using the vendor's data, in the vendor's preferred sequence. A POC designed that way is just a paid demo.
The failures that sink enterprise IT deployments are never tested in a vendor-designed POC: the integration that breaks with your IdP, the performance cliff at 1,400 concurrent users, the audit log format your SIEM can't parse. They surface six months into implementation, when you're contractually committed.
FYI, if you're still building your IT vendor shortlist before reaching the POC stage, we can help. Tell us your requirements and we'll send a vetted list of vendors worth your time. We'll prep the vendors before the call so your conversation starts from context.
Design the POC Around Your Failure Scenarios, Not the Vendor's Use Cases

An adversarial POC is designed by you, run in your environment, and tests the scenarios where the product is most likely to fail in your specific context.
Pull your last three major incidents. Pull the finding from your last compliance audit. Pull the integration that caused the most pain in your last platform migration. These become your POC test scenarios, not the use cases in the vendor's solution brief.
By IT product category, the scenarios that matter most:
- Security tooling (EDR, SIEM, CASB, PAM): Does the product detect credential theft and lateral movement in your Active Directory environment, or just generic malware? Vendors demo the latter. You need to test the former.
- Backup and recovery platforms: Does the product give you a defensible clean recovery point after a 30-day attacker dormancy period, not just a clean restore from yesterday's snapshot?
- Infrastructure and cloud management: Does the product handle the workload that doesn't fit the standard deployment pattern, such as the legacy Oracle instance on bare metal or the NAS shares that predate your current team?
- ITSM and observability: Does the product work under 3am P1 conditions, when three on-call engineers need to correlate events across six systems simultaneously?
For a broader view of the questions that should shape your evaluation before the POC starts, the top questions about vendor selection in IT covers the pre-POC framework in detail.
Before You Brief the Vendor: Three Things to Lock Down
1. Write your success criteria before the vendor briefing
Success criteria written after you've seen the vendor's demo are shaped by what you've already seen. Write them before the first POC conversation and share them with the vendor at kickoff. Every criterion needs a number, a format, or a binary condition:
2. Establish who controls the test environment
You do. State this at the POC kickoff meeting:
- You hold admin credentials. The vendor gets a named account with standard post-deployment admin permissions, not superuser access.
- All configuration changes are documented, approved by your team, and logged before implementation. No undocumented changes between test runs.
- At least half of test sessions run without the vendor present. Attended sessions are for questions. Unattended sessions show you what the product does when nobody is performing.
- You use your own data. Anonymized or synthetic, but mirroring your production data structure and volume, not the vendor's sample dataset.
3. Set the time boundary at kickoff
Two to four weeks for most enterprise IT vendor POCs. Six weeks maximum for complex infrastructure deployments with multiple integration points.
If the vendor requests an extension, that is a finding. Either the product is harder to deploy than represented, or the vendor needs more time to pass your tests.
The Five Technical Dimensions Every IT Vendor POC Must Test
1. Core functionality against your documented requirements
Each requirement gets a pass/fail score with documented evidence: a log file, a timestamped screenshot, a screen recording. The requirements most IT teams under-document and then regret:
- RBAC granularity: Does the access control model map to your actual org structure, or does it force compromises that create security gaps?
- Multi-tenancy and environment separation: Can you isolate dev, test, and production natively, or only through workarounds?
- Data residency: Where does the data actually live? Which sub-processors handle your data and in which geographies?
- API completeness: Does the API cover the operations you need to automate, or are critical functions only available through the UI?
If you don't have a documented requirements list yet, 10 questions every IT leader should ask before choosing a vendor is a good starting point before the POC begins.
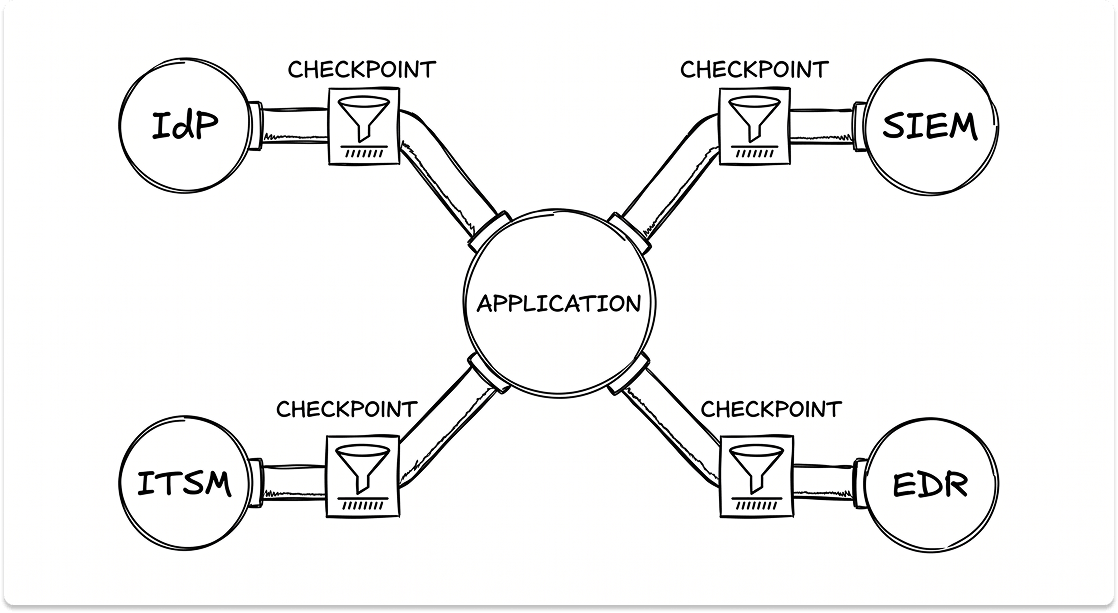
2. Integration with your specific stack
Not a clean API call to a test endpoint. Actual integrations with the systems that will connect to this product in production.
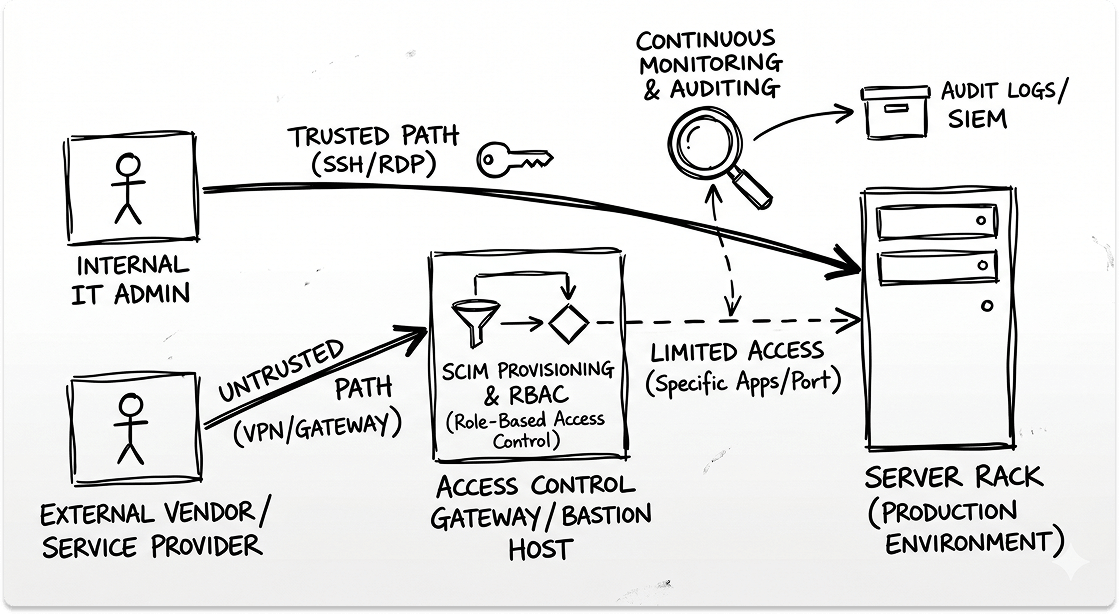
Identity and access management: Test SSO via your IdP (Okta, Microsoft Entra ID, Ping Identity), SCIM provisioning, and de-provisioning. When you disable a user in your IdP, how long before access is revoked in the vendor's system? For PAM and security tooling, minutes is a gap. Hours is a critical finding.
SIEM integration: Does the product emit logs in a format your SIEM ingests natively, or do you need a custom parser? Test with your actual SIEM, whether that's Splunk, Microsoft Sentinel, Elastic, or CrowdStrike Falcon LogScale. A SIEM integration requiring a custom parser is a maintenance liability that compounds every time the vendor updates their log schema.
Ticketing and ITSM: Test the ServiceNow or Jira Service Management integration end to end. Does it deduplicate alerts or create one ticket per event? The answer determines whether your on-call team wakes up to three tickets or three hundred.
Existing security tooling: Agent conflicts between an EDR and a new security tool that surface in a POC take a day to resolve. The same conflict in production takes weeks and creates coverage gaps.
3. Performance under realistic load
Establish these numbers before the POC starts, then run the load test without telling the vendor when:
- Concurrent user count at peak, not average
- Daily active alert or event volume for security and observability tooling
- Data ingestion rate per hour for SIEM and backup platforms
- API call volume per hour for platforms your automation will hit
- Storage growth rate per month for backup and data protection platforms
4. Security and compliance posture
Test against your specific obligations, whether that's SOC 2, HIPAA, PCI-DSS, ISO 27001, or FedRAMP, not generic best practices.
Audit log integrity: Export the audit log for the test period and attempt to delete or modify an entry. Verify the claim that it is not possible rather than accepting it at face value.
Encryption and key management: Confirm whether you control the encryption keys or the vendor does. For regulated industries, customer-managed encryption keys (CMEK) are increasingly a hard requirement from auditors and cyber insurers.
Vulnerability disclosure cadence: Ask for the last three CVE notifications and the time between disclosure and patch availability. A vendor who can't produce this data doesn't have a mature vulnerability management process.
Penetration test results: Request the most recent independent pen test report with findings and remediation status under NDA. A vendor who refuses has findings they don't want you to see.
5. Failure behavior and operational recovery
Simulate specific failure conditions during the POC:
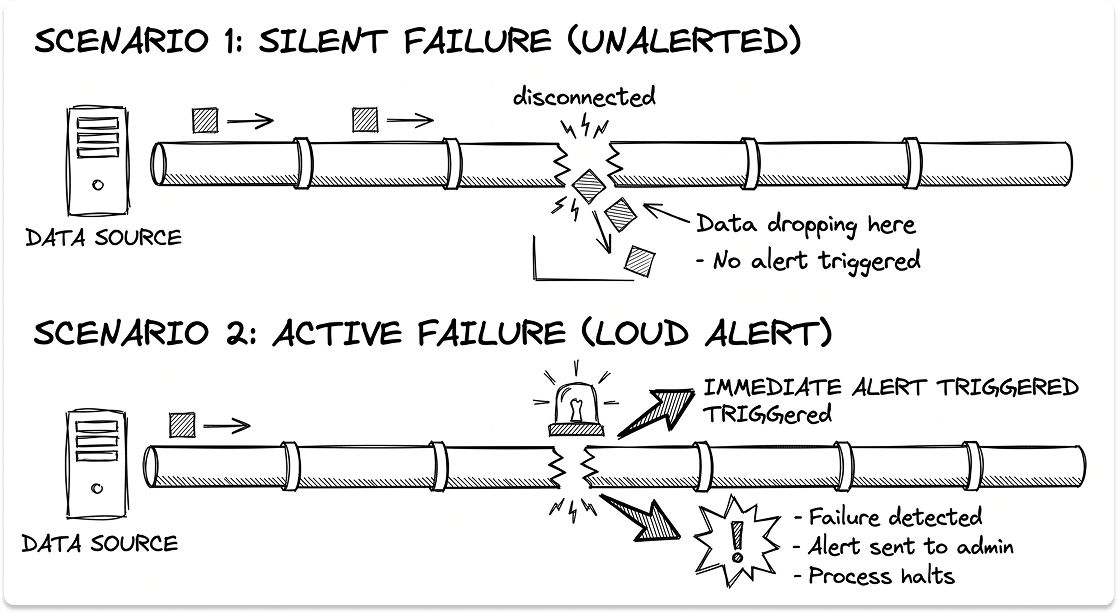
Dependency failure mid-operation: Kill the network connection during a backup job. Stop log ingestion from one source and test whether the platform alerts on the gap or silently drops events. Silent failures in security and backup tooling are a critical finding.
Credential compromise simulation: Revoke the service account the product uses to connect to a dependency. Does it fail loudly with an alert, or silently in a degraded state?
P1 support response: Open a genuine P1 ticket during the POC and measure time to a technically capable engineer who can advance the issue, not time to first response. The support you receive during a POC is the best support you will ever receive from that vendor.
Configuration rollback: Make a deliberate misconfiguration that breaks a core function. Is there a configuration audit trail? How does rollback work? A product with no rollback mechanism and no configuration history is an operational risk in any environment where multiple admins have write access.
The IT Vendor POC Scorecard
Hard stop rule: Any dimension that fails its pass threshold is a disqualifying finding regardless of total score. A vendor scoring 94% overall with an unresolved critical security finding does not pass the POC.
How to Respond to a Failed POC Finding
Fixable gap with a committed roadmap: Acceptable if the gap risk during that period is manageable, and if the commitment means a remedy clause with a financial consequence, not a slide in a deck.
Architectural limitation: Not fixable in any relevant timeframe. End the evaluation. Continuing in the hope it resolves is how bad contracts get signed.
Operational and support failure: The support you receive during the POC is the best you will ever receive from that vendor. Model what it looks like 18 months post-sale.
Vendor behavior under pressure: A vendor who responds to a failed finding by reframing the test criteria rather than addressing the gap is showing you how they will behave in every contract dispute and renewal negotiation.
Using IT Vendor POC Findings in Contract Negotiations
Your POC documentation is your contract negotiation brief. Every borderline finding becomes a specific contractual obligation. A performance benchmark that barely passed becomes a minimum SLA with a remedy clause. An integration that required manual workarounds becomes an implementation milestone with a sign-off gate before go-live.
Vendors who push back on POC-derived contract terms are signaling they don't intend to meet them post-sale.
For a broader framework on what to negotiate before signing, the complete guide to IT vendor selection covers the commercial and technical dimensions in detail. If you're still building your vendor list and haven't reached the POC stage yet, how and where to find IT vendors and solutions is the right starting point.
When a Formal IT Vendor POC Is Worth Running
A structured POC is worth the investment when:
- The contract value is significant enough that a failed implementation has material financial or operational consequences
- The product integrates with core infrastructure (identity, security stack, data layer) where compatibility failures are expensive to unwind
- Your compliance obligations require documented evidence of pre-purchase technical evaluation
- You're replacing a deeply embedded platform where switching costs are high
- You're evaluating two or more vendors and need comparable evidence to support the selection decision
A full structured POC may be disproportionate when:
- The product has a narrow, well-defined scope with low integration complexity
- You have strong peer reference evidence from organizations with identical environments and requirements
- A time-limited trial with your own data and a defined evaluation checklist provides sufficient evidence at lower operational cost
Before you get to the PoC, we can help evaluate vendors
If you're evaluating IT vendors and want help building a shortlist before you reach the POC stage, we can help. Tell us your requirements and we'll send a vetted list of vendors worth your time. We'll prep the vendors before the call so your conversation starts from context.
FAQ
What is an IT vendor proof of concept?
An IT vendor proof of concept is a structured technical evaluation where an IT leader tests a vendor's product in a controlled environment against their specific requirements, integration dependencies, and failure scenarios before committing to a contract.
How long should an IT vendor POC take?
Two to four weeks for most enterprise IT vendor POCs. Complex infrastructure deployments with multiple integration points can run to six weeks with a clear milestone structure. POCs that extend beyond six weeks without justification indicate that the product is harder to deploy than represented, or that the vendor is managing your evaluation timeline.
What is the difference between a POC and a pilot?
A POC tests whether the product meets your technical requirements in a controlled environment. A pilot deploys the product to a subset of production users or workloads to validate operational behavior at scale. A POC should always precede a pilot.
Who should be involved in an IT vendor POC?
The IT leader or procurement lead who owns the decision. The infrastructure or security engineer who will manage the product post-deployment. The compliance or security officer if the product handles regulated data. At least one end user who will use the product daily. The vendor's SE for technical questions, not to narrate test sessions.
Should you run POCs with multiple vendors simultaneously?
Yes, if you have the capacity. Parallel POCs run identical scenarios against multiple vendors on the same timeline and produce directly comparable findings. Sequential POCs introduce evaluation drift as your expectations shift between vendors. If you must run sequentially, lock the success criteria before the first POC and don't revise them between vendors.
What does it mean if a vendor refuses a structured POC?
A vendor who declines a buyer-controlled POC and insists on a vendor-run evaluation knows their product won't pass your tests.
What is the difference between a POC and a vendor demo?
A vendor demo shows you what the product does under the vendor's control, using the vendor's data. A POC tests whether it works in your environment, under your conditions, against your failure scenarios.