IT Vendor Management Process: Definition, Lifecycle & Best Practices
IT vendor management is the process of selecting and optimizing tech vendors. This guide details the 7-stage lifecycle, core components, challenges, risks, and best practices.

In my experience, IT leaders no longer simply buy hardware servers or renew perpetual software licenses on a multi-year cycle. Tech stacks today are interconnected ecosystem of hundreds of third-party applications, cloud infrastructure providers, and managed services.
Managing this massive ecosystem requires a highly disciplined IT vendor management process. When your execution is poor, you face overlapping software costs, severe security blind spots, and compliance failures.
When your execution is precise, you turn third-party vendor relationships into operational advantages that drive measurable business outcomes and protect your organization from external threats. To truly master this domain, you must understand the hidden frameworks and blind spots that catch most organizations off guard.
This comprehensive guide breaks down exactly how to build, implement, and scale an effective IT vendor management strategy from the ground up, serving as your core operational playbook.
What is IT Vendor Management?
IT vendor management is the continuous operational discipline of selecting, onboarding, monitoring, and optimizing the third-party technology providers that service your organization. This umbrella covers software-as-a-service platforms, cloud hosting environments, cybersecurity tools, external development partners, and hardware suppliers.
Strategic IT Vendor Management vs. Traditional Procurement
Traditional procurement is a highly transactional function. It focuses heavily on the initial deal. Procurement teams negotiate the price, sign the contract, process the purchase order, and move on to the next ticket. It is an episodic, cost-driven event.
Strategic IT vendor management is relational and continuous. It focuses on the entire lifecycle of the technology. You must ensure the vendor delivers on their initial promises, monitor their security posture over time, optimize licensing costs based on actual employee usage, and hold them accountable for their service level agreements. This shift transforms the IT department from a simple gatekeeper into a strategic gateway for the business.
The Four Pillars of IT Vendor Management
A robust enterprise program rests on four operational pillars. If any of these pillars are weak, your entire software supply chain is at risk.
%20(1).png)
Why IT Vendor Management Matters
Cost control is the most obvious benefit. Structured oversight eliminates duplicate tools, terminates zombie accounts, and right-sizes licenses based on actual usage. Organizations that implement a structured program typically recover massive amounts of wasted budget in their first year.
However, the most critical factor for modern IT leaders is risk reduction. Strong vendor management protects your environment from third-party breaches, maintains compliance with regulatory frameworks like SOC 2 and HIPAA, prevents vendor lock-in, and monitors the financial stability of your partners to avoid sudden service disruptions.
The Core IT Vendor Management Process
Designing an Effective Vendor Management Workflow
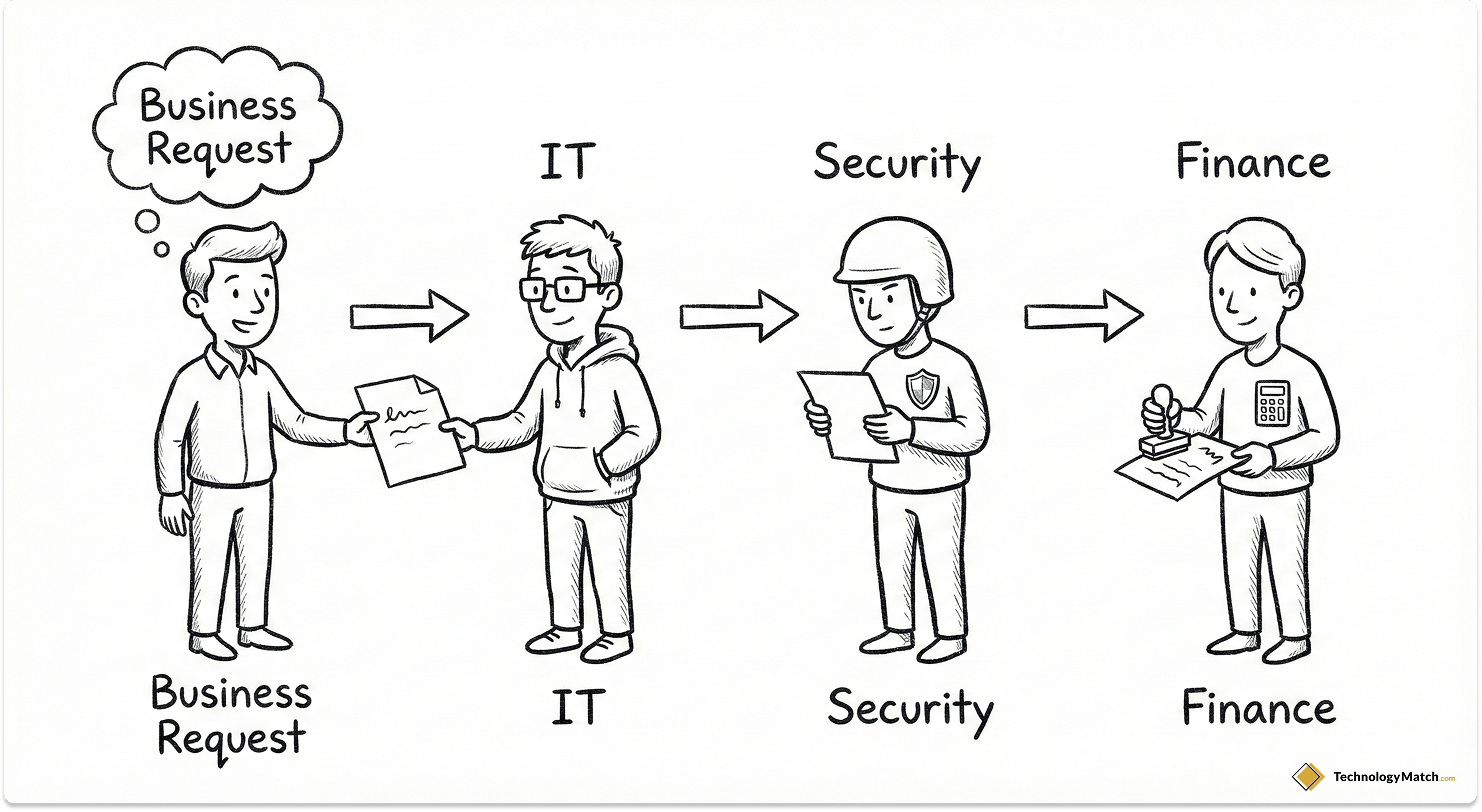
An effective vendor management workflow requires clear routing and strict governance. You cannot allow individual departments to purchase and deploy software independently. When a department requests a new tool, the request must follow a standardized, documented path.
First, the business unit submits an intake form detailing the exact business problem, the required capabilities, and the proposed budget. Next, IT reviews the request to ensure the tool aligns with the current enterprise architecture and checks the existing catalog to see if an internal solution already exists.
If IT approves, InfoSec conducts a rigorous security audit to assess how the vendor handles corporate data. Following security approval, Finance validates the budget allocation. Finally, Legal reviews the terms of service and liability clauses. Centralizing this workflow prevents rogue purchasing and ensures all stakeholders sign off before a single line of code is integrated into your environment.
Roles & Governance: Who Owns the Process?
Accountability must be explicit. Without clear ownership, vendor management devolves into chaos. Many mature organizations choose to formalize this structure by building a dedicated IT Vendor Management Office (VMO).
The Chief Information Officer sets the overarching vendor strategy and gives final approval for strategic, high-cost vendors. Dedicated IT Vendor Managers handle the day-to-day lifecycle operations, maintain the contract repository, and track performance metrics.
Individual department heads act as the business owners. They are responsible for defining the technical requirements, driving user adoption within their respective teams, and confirming that the software actually solves the initial business problem. InfoSec and Legal act as the ultimate authorities on risk and compliance.
The 7-Stage IT Vendor Management Lifecycle
An effective program follows a highly structured sequence. Skipping any of these phases introduces unnecessary risk and financial waste into your organization. For a deeper dive into operationalizing these steps, review our practical guide to the vendor management lifecycle.

Phase 1: Discovery & Vendor Intake
Before you buy new software, you must know exactly what you already have. You must hunt down shadow IT. These are the unapproved tools employees purchase with corporate credit cards to bypass IT bottlenecks.
Use single sign-on logs, finance expense reports, and specialized browser extensions to identify these hidden applications. Once you have a clear inventory, establish a standardized intake process. Force employees to document the business need, the expected data sensitivity, and the required timeline before they begin talking to sales representatives.
Phase 2: Vendor Selection & Technical Due Diligence
A rigorous vendor selection process translates abstract business needs into weighted, testable criteria. You must script product demonstrations around real user journeys rather than allowing the vendor to show you highly polished, irrelevant features.
Security due diligence is mandatory in this phase. IT leaders frequently cite third-party vulnerabilities as their primary cybersecurity fear. You must look beyond the marketing material. Validate SOC 2 Type II reports, demand recent penetration test results, and scrutinize their historical incident logs. You must also ask about their fourth-party risk. Who are their vendors, and how are they securing your data?
To accelerate this phase, I advise teams to leverage curated networks like TechnologyMatch.com. Using a pre-vetted marketplace reduces the overwhelming burden of manual due diligence and helps you build a highly targeted shortlist of reliable IT partners based on your specific architectural requirements.
Phase 3: Contract Negotiation & Price Benchmarking
Never accept the initial pricing model. You must use price benchmarking data to understand the true market rate for the software. Project your actual usage over a three-year period to right-size your licenses from day one.
When negotiating, you must secure specific contractual protections. Demand volume discounts for multi-year commitments and tiered pricing that scales down as your usage increases. You must implement strict service level agreement penalty clauses. If the vendor fails to meet their uptime guarantees, they must issue automatic financial credits to your account.
Crucially, you must explicitly opt out of auto-renewal clauses. Vendors use auto-renewals to lock you into another year of service before you have the chance to evaluate their performance. Implement price protection caps to ensure they cannot raise your rates by more than a small, fixed percentage at the end of the term.
Phase 4: Vendor Onboarding & Integration
The onboarding phase dictates the long-term success of the deployment. You must configure single sign-on and automate user provisioning via SCIM protocols immediately. Never rely on manual account creation. Implement strict role-based access control to ensure employees only have access to the data they need to perform their jobs.
Map out all data flows between the new vendor and your existing technology stack. Set up integrations through secure APIs and validate that all security controls are functioning correctly. Before full deployment, execute a formal go-live checklist that requires final, documented sign-off from InfoSec, Legal, Finance, and the business owner.
Phase 5: Performance Management & Regular QBRs
You must track reliability metrics aggressively. Monitor system uptime, incident frequency, and the speed at which the vendor resolves critical support tickets. Apply your service credits immediately when targets are missed. Do not wait for the vendor to offer them.
For your most critical, high-cost strategic vendors, you must mandate a Quarterly Business Review. A proper QBR is not a sales pitch for new features. It is a data-driven operational meeting. Review their performance data over the last ninety days, discuss persistent technical issues, review their upcoming product roadmap, and identify specific opportunities to optimize your current licensing costs.
Phase 6: Ongoing Risk & Compliance Monitoring
Security is not a static checklist completed during the selection phase. The threat landscape evolves daily. You must implement continuous risk monitoring.
Track public vulnerability disclosures, sub-processor changes, and SSL certificate expirations continuously. Use security rating platforms to monitor the vendor's external security posture in real time. Connect this risk data directly to your daily operations. If a vendor experiences repeated security incidents or fails to patch known vulnerabilities promptly, you must pause all expansion plans and consider restricting their access to your network until they remediate the core issue.
Phase 7: IT Vendor Offboarding, Renewals, and Renegotiation
Begin your renewal evaluations exactly ninety days before the contract expires. Pull your performance data, gather stakeholder feedback, and benchmark their current pricing against competitors. Make a firm decision to renew, renegotiate, or replace.
If you decide to terminate the relationship, you must execute a strict vendor offboarding protocol. Many organizations fail here, leaving active data connections open for months after a contract ends. You must revoke all system access by disabling their connections in your identity provider. You must immediately revoke all API keys and OAuth tokens. Extract your proprietary data in a usable format, settle all final invoices, and demand a verified data deletion certificate from the vendor's legal team.
Top IT Vendor Management Best Practices for 2026
Adopting the right strategy is the difference between controlling your software stack and letting it control you. You should implement these core vendor management best practices immediately.
Create a Single Source of Truth
Store all contracts, security audits, compliance certificates, and performance metrics in one centralized repository. Managing vendor relationships across fragmented spreadsheets and disparate email threads is a massive operational liability. A single source of truth ensures that anyone in IT, Finance, or Legal can instantly access the current status of any vendor.
Implement Risk-Based Vendor Tiering
Not all vendors require the same level of oversight. You must classify your vendors into three distinct tiers to allocate your resources effectively.

- Strategic Vendors: These are high-cost, mission-critical platforms that handle sensitive data. They require deep technical due diligence, custom contract negotiations, and mandatory Quarterly Business Reviews.
- Tactical Vendors: These are important operational tools that handle internal data. They require standard security vetting and semi-annual performance check-ins.
- Operational Vendors: These are low-cost, low-risk utilities. They require minimal vetting and rely on automated monitoring rather than manual oversight.
Automate Renewal Alerts and Workflows
Missing a cancellation window is an unacceptable financial error. You must configure automated alerts at the ninety, sixty, and thirty-day marks before any contract expires. This gives your team the necessary runway to evaluate performance, explore alternatives, and build a strong negotiation strategy.
Prioritize SaaS Vendor Management
Software-as-a-service applications require highly specialized oversight. Because the barrier to entry is so low, employees can purchase and deploy SaaS tools independently within minutes. You must run frequent discovery audits to catch unapproved applications, consolidate duplicate tools, and eliminate zombie accounts belonging to former employees.
Overcoming Common IT Vendor Challenges
Even the most mature IT departments face operational roadblocks. You must be prepared to solve the top IT vendor management challenges proactively.
Resource Constraints & Fragmented Data
Managing fifty or more active vendors with a lean IT team is nearly impossible when your data is scattered across legal network drives and finance inboxes. Without a single source of truth, answering basic questions requires manual detective work. Centralizing this data removes the administrative burden and allows your team to focus on strategic negotiation rather than chasing down PDF contracts.
Shadow IT & SaaS Sprawl
When departments buy tools independently, you create severe security blind spots and waste massive amounts of budget on redundant capabilities. You must enforce strict single sign-on policies. If an application is not behind your corporate SSO, it cannot be used. This instantly forces visibility over what applications are actually interacting with your corporate data.
Vendor Fatigue & Reactive Risk
Sending a massive, two-hundred-question security spreadsheet to every minor vendor creates severe bottleneck delays for the business. You must transition to a proactive model. Use continuous security rating platforms and rely on standardized shared trust portals to accelerate the vetting process without compromising your security posture.
IT Vendor Management Technology & Software
To scale these processes, you must invest in purpose-built vendor management technology. The average enterprise utilizes a combination of the following platforms. For a comprehensive comparison of vendors in this space, consult our guide on the best vendor management software for IT leaders.

SaaS Management Platforms
These specialized tools connect directly to your identity provider and your financial expense systems. They automatically discover unapproved software purchases, track active user login rates, and highlight wasted spend across your entire SaaS portfolio.
IT Service Management Tools
Your ITSM platform handles the ticketing and internal routing for new vendor requests. It ensures that the proper approval workflows are strictly followed and documented before any new software is integrated into your environment.
Governance, Risk & Compliance Software
GRC platforms automate the tedious security questionnaire process. They track third-party compliance status against regulatory frameworks like HIPAA, SOC 2, or GDPR, and provide automated alerts when a vendor's certification is close to expiring.
Measuring Success: IT Vendor Performance Metrics
You must measure the success of your program using objective data. Relying on gut feelings during renewal conversations puts you at a severe disadvantage. To structure your reporting, implement our recommended vendor management KPIs and frameworks.

Uptime, SLA Compliance, and MTTR
You must track core system reliability. Monitor the exact system uptime percentage, the frequency at which the vendor meets their service level agreements, and their Mean Time to Resolution for critical severity-one support tickets. If the vendor consistently violates these metrics, you have the data required to demand service credits or terminate the contract for cause.
Adoption Rates & Cost per Active User
Software holds zero value if your employees refuse to use it. You must track the percentage of provisioned licenses that are actively logging into the platform on a monthly basis. Calculate the true cost per active user. If you are paying for one thousand licenses but only three hundred employees log in, you must aggressively downsize your contract during the next renewal cycle.
IT Vendor Management Process Checklist
Use this actionable framework to standardize your approach to every new technology purchase.
For further clarification on complex procurement scenarios, read our breakdown of the 10 most important questions about vendor management.
Closing Thoughts
The days of treating software procurement as a simple administrative task are over. In my experience advising enterprise teams, I have seen firsthand how an unmanaged technology stack leads directly to bloated contracts and severe security vulnerabilities. If you fail to manage your vendors, they will inevitably manage you.
By implementing the strict, 7-stage vendor lifecycle outlined in this playbook, you transform a reactive procurement function into a proactive operational advantage.
When you build a disciplined framework, you regain absolute control over your budget, your security posture, and your overall operational resilience.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What is IT vendor management?
IT vendor management is the systematic process of selecting, onboarding, monitoring, and optimizing third-party technology vendors who provide products or services to your organization. It encompasses contracts, performance, relationships, and risk management.
What are the steps in the IT vendor management process?
The IT vendor management lifecycle includes: (1) Discovery & Intake, (2) Vendor Selection & Due Diligence, (3) Contract Negotiation, (4) Onboarding & Integration, (5) Performance Management, (6) Risk & Compliance Monitoring, and (7) Renewal or Offboarding.
Why is IT vendor management important?
IT vendor management reduces risk, controls costs, improves speed, raises quality, aligns stakeholders, and enables innovation through strategic vendor partnerships.
How do you measure vendor performance?
Track IT vendor management metrics like SLA compliance rate, MTTR, cost per active user, adoption/utilization rate, vendor compliance score, security incident frequency, renewal on-time rate, and renewal savings percentage.