How to choose the right IT vendor or Partner Using a Framework
Learn what vendor selection is, the 5 phases, how to get a trusted vendor, how to analyze with criteria and scorecards, and the key factor behind the right choice.

Choosing the wrong IT vendor breaks your budget and exposes your proprietary data. You cannot rely on polished sales presentations and unverified product claims. You need a structured operational model to evaluate technical fit, security posture, and longterm financial viability.
The average enterprise wastes thousands of dollars annually on unused software licenses and redundant tools. I use a vendor selection framework to evaluate and onboard all new technology partners. This methodology strips away marketing noise and forces vendors to prove their value against your exact business constraints. It integrates perfectly with your broader IT vendor management framework.
The High Cost of Poor IT Vendor Selection
Poor vendor selection drains your budget and creates massive security blind spots. When you buy software based on charisma instead of evidence, you inherit technical debt. The financial damage is measurable and severe. Organizations routinely carry hundreds of SaaS applications and waste over $135,000 per year on unused or underutilized licenses.
Beyond wasted spend, you face severe operational risks. According to Gartner research, more than 60 percent of vendor-related disruptions originate from fourth-party dependencies. If you fail to evaluate those dependencies upfront, your operations will halt when a sub-vendor goes offline. The evidence-based vendor selection framework acts as the antidote to these failures. It replaces assumptions with hard data.
What Is the IT Vendor Selection Process?
The IT vendor selection process is the structured method you use to identify, evaluate, and engage external suppliers. You evaluate these suppliers to ensure they align directly with your business strategy, risk posture, and operating realities.
This is not a standard procurement exercise focused on finding the lowest price. A true IT vendor selection requires you to measure technical fit, demand hard security evidence, and enforce strict vendor accountability. A mature vendor selection process acts as the foundation for your ongoing contracts, service level agreements, and daily governance.
5 Phases of an Effective Vendor Selection Framework
I break the vendor selection framework into five disciplined phases. Every phase includes strict decision gates to keep your evaluations objective and tied to real business outcomes.
Phase 1: Define Outcomes and Set Vendor Selection Criteria

You must translate your business strategy into measurable needs before you talk to a single sales representative. Start by defining your goals, technical constraints, timeline, and absolute budget.
Form a cross-functional buying committee that includes IT, security, procurement, finance, legal, and your core end users. If you leave security or legal out of this initial phase, you will face massive delays right before you try to sign a contract. Assign a single process owner to drive the decision forward and establish a clear RACI matrix.
Finally, translate your goals into weighted vendor selection criteria. Separate your absolute must-haves from your nice-to-haves and deal-breakers immediately. Specify the exact artifacts you will require, such as audit reports, architecture documentation, and uptime histories. This creates an objective standard for the rest of the project.
Phase 2: Vendor Discovery and Rapid Qualification

Do not rely on cold outreach or generic web searches for vendor discovery. Use trusted analyst research, peer referrals, vetted directories, and curated matchmaking platforms to build your initial longlist. This targeted approach prevents you from wasting time on misaligned products.
Once you have a list, qualify the companies fast. Screen out vendors who fail your absolute non-negotiables regarding security posture, integration fit, or budget constraints. Map their stated capabilities directly to your vendor selection criteria to drop the weak candidates early. Gather high-signal evidence immediately. Request referenceable results, security control summaries, and technical architecture overviews. Exit this phase with a tight shortlist of three to five credible vendors accompanied by a preliminary risk flag assessment.
Phase 3: Structured Vendor Evaluation via RFI and RFP

You need clear comparisons to make smart financial decisions. Convert your business requirements into a structured Request for Proposal (RFP) or Request for Information.
Force the vendors to use consistent formats for their pricing units, SLAs, and security controls. Use templates so your vendor evaluation remains comparable and fully auditable. Tell them exactly how you will score their responses and publish the weights upfront for transparency. This keeps the vendors focused on your actual needs.
Score the responses independently first. Calibrate your scores as a group to remove individual bias and capture any remaining capability gaps for follow-up questioning. You should exit this phase with a ranked list of responses and a clear mathematical delta between your options.
Phase 4: Scenario-Based Demos and Deep Due Diligence

Never accept a generic product tour. Sales engineers design standard demos to hide product flaws and highlight flashy interface elements. You must script your demos and Proof of Concepts around your highest-value workflows, your complex integrations, and your specific failure modes.
Give the vendor your test data. Ask them to show you exactly how the product handles a failed API call or a massive data spike. Define clear pass and fail gates, along with key performance indicators, before the vendor starts the demonstration. Capture hard artifacts during these tests. Save the test plans, system logs, and final results to build your evidence pack.
This phase is where you execute deep due diligence to validate marketing claims under real conditions. You must review the following items carefully.
Security, Privacy, and Compliance
Do not assume a vendor is secure just because they list popular logos on their website. Request actual SOC 2 or ISO 27001 audit reports, recent penetration test summaries, and data processing agreements. Review their historical incident logs. You must confirm their list of subprocessors to understand your fourth-party risk exposure. Ask them to walk you through their exact breach response procedures. Security proof is a mandatory gate in the IT vendor selection process.
Reliability and Support
A product is useless if your team cannot access it. Validate their historical uptime, service level objectives, recovery time objectives, and support escalation paths. Do not just look at their marketing numbers. Check their public status pages and read their root cause analyses. You need to see how they behave and communicate under the stress of a live outage.
Total Cost of Ownership (TCO) Modeling
Software licenses are only a fraction of the total cost. Map the proposed pricing to your real usage over a three-year timeline. Include projected growth, data overages, integration engineering work, and internal support costs. Stress-test their renewal terms. A transparent financial model keeps the vendor evaluation grounded in real value.
References and Business Viability
Never call the hand-picked reference the sales rep offers you first. Ask to speak directly to customers operating in a similar regulatory context with a similar technology stack. Ask those references about the surprises that popped up after go-live. Ask how the vendor handles support tickets. Finally, assess the vendor's financial health, customer concentration, and leadership stability. You must verify they will survive the duration of your contract.
Phase 5: The Defensible Decision, Negotiation, and Onboarding
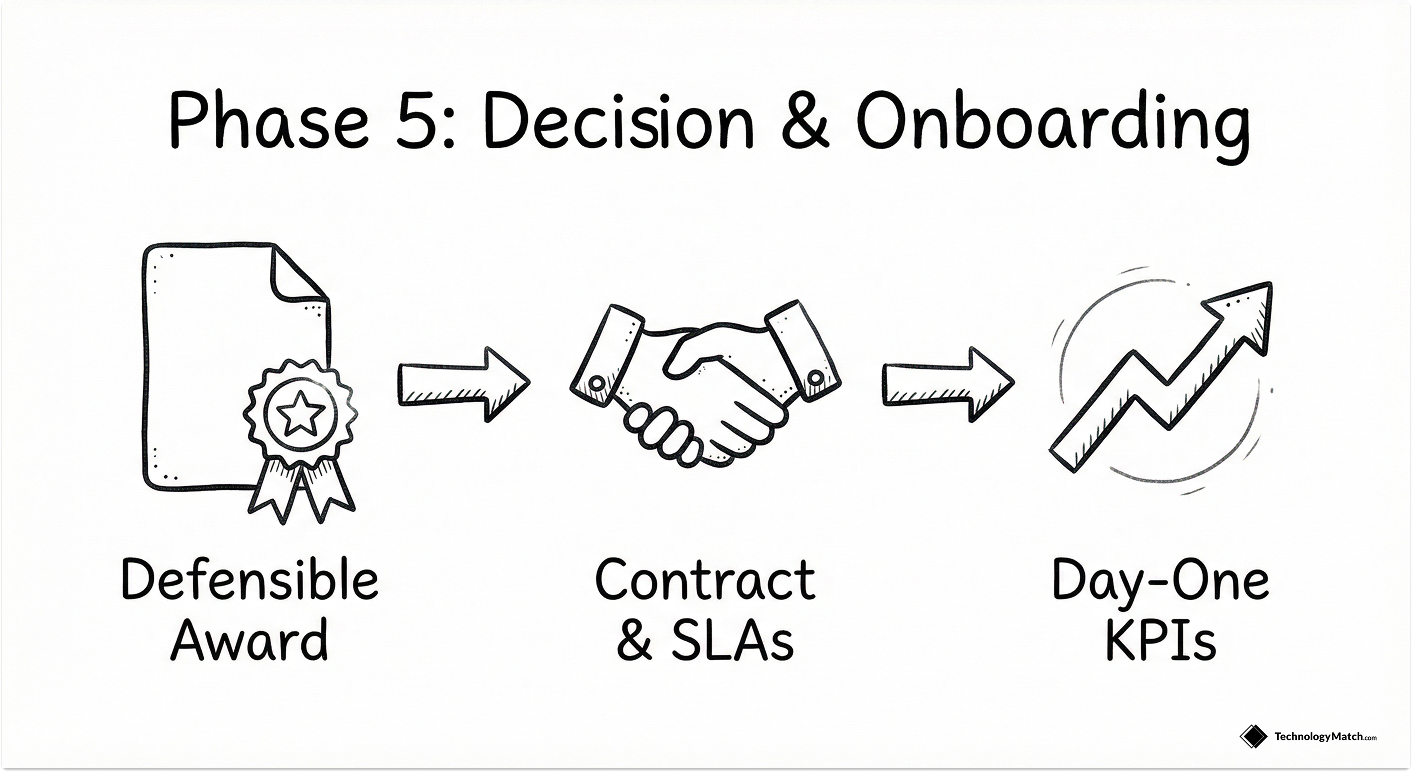
Apply your minimum thresholds and the weighted scorecard to make a defensible award. Document your rationale and archive all artifacts, logs, and scoring matrices to a central decision record. Share this decision pack with your stakeholders. Defensibility is a core feature of proper IT vendor selection. It protects you during future audits.
Next, you move to the contract phase. Convert your winning vendor selection criteria directly into your contract terms. Lock in strict service level agreements, specific service credits for downtime, and ironclad pricing protections. Define your exit timelines and hand-back obligations clearly.
Phase your delivery. Tie your financial payments to specific implementation milestones rather than paying entirely upfront. Negotiation should mirror your earlier analysis, not restart it.
Finally, maintain operational continuity. Hand off your evaluation scorecard to your onboarding and delivery teams. Instruct them to use these exact metrics as day-one key performance indicators. Baseline the initial performance, schedule your first quarterly business review, and maintain a strict feedback loop.
Building a Weighted Vendor Selection Criteria Scorecard
A weighted scorecard is your best defense against sales charisma. If you treat every feature as equally important, you will make the wrong choice. Group your vendor selection criteria into specific categories and assign mathematical weights reflecting their true impact on your business outcomes.
I evaluate IT vendors across these specific, critical categories:
The Most Important Factor in IT Vendor Selection
The most important factor in any IT vendor selection is clear, objective evidence. You must build weighted, evidence-backed vendor selection criteria tied directly to your business outcomes and risk profile.
Precise criteria focus your vendor discovery, force strict apples-to-apples comparisons, and expose operational trade-offs early in the buying cycle. You reward actual proof, not storytelling.
This discipline compounds over time. Your IT vendor selection process gets faster each cycle, your onboarding becomes smoother, and your long-term governance stays aligned with your original strategic goals. Your criteria act as the backbone that turns a simple software purchase into sustained business value.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What is vendor selection?
Vendor selection is a structured, criteria-driven process organizations use to identify, evaluate, and engage external suppliers. It aligns purchases directly with business outcomes and risk profiles using hard evidence rather than marketing claims.
What are the 5 phases of vendor selection?
The five phases of the vendor selection process are: defining outcomes and aligning stakeholders, discovering and qualifying vendors, running a structured RFI/RFP, executing scenario-based demos and due diligence, and making the decision to negotiate and onboard.
How do you execute proper vendor discovery?
Source from credible channels like peer referrals, analyst research, vetted directories, and curated matchmaking platforms. Avoid cold scattering and quickly drop vendors who fail your absolute non-negotiable requirements regarding security and budget.
How do you measure vendor viability during an evaluation?
You assess viability by reviewing the vendor's financial health, leadership stability, customer concentration, and overall product roadmap transparency. This ensures the partner is resilient enough to support your long-term operations.