The Vendor Onboarding Process: 5 Stages, Best Practices, and a Checklist for IT Teams
A stage-by-stage breakdown of the vendor onboarding process for IT teams: risk tiering, compliance documentation by vendor type, IT security review checklist, contract approval sequencing, and benchmark timelines for Tier 1, 2, and 3 vendors

Manual vendor onboarding costs more than $35,000 per supplier. Automated onboarding brings that figure below $2,500. The gap is not a technology problem. It is a process problem, and it starts on day one.
Every vendor your organization adds is a potential access point, compliance liability, or financial exposure if onboarded without structure. 30% of all data breaches in 2024 involved a third-party vendor, double the rate from the year before.
The breach often does not happen at the point of entry. It happens inside a relationship that was already running, with a vendor that was cleared during a process that skipped the controls that mattered.
Vendor onboarding is the structured process of qualifying, documenting, integrating, and activating a third-party vendor before they access your systems, data, or payment infrastructure.
For IT leaders, it is also the first line of defense in your third-party risk posture. What follows is a stage-by-stage breakdown of how to run the supplier onboarding process correctly, what documents to collect by vendor type, and what IT specifically needs to own at each step.
FYI, if you're looking for IT vendors to work with, we can help. Tell us your requirements and we will find vendors that fit. If you're willing to move forward, we will prep them before your meeting so you conversation can start with context.
Please take this survey so we can get to know you better + book a meeting to get started. And it's free.
What the Vendor Onboarding Process Actually Involves for IT
Every other guide treats the supplier onboarding process as a procurement workflow with an IT checkbox at the end. That framing is why compliance gaps persist.
In practice, three parallel tracks run through every new vendor engagement simultaneously:
- Procurement track: business need validation, commercial negotiation, payment setup, and contract execution
- Compliance track: documentation collection, risk assessment, regulatory alignment, and audit readiness
- IT/InfoSec track: access provisioning, integration testing, security configuration, and monitoring setup
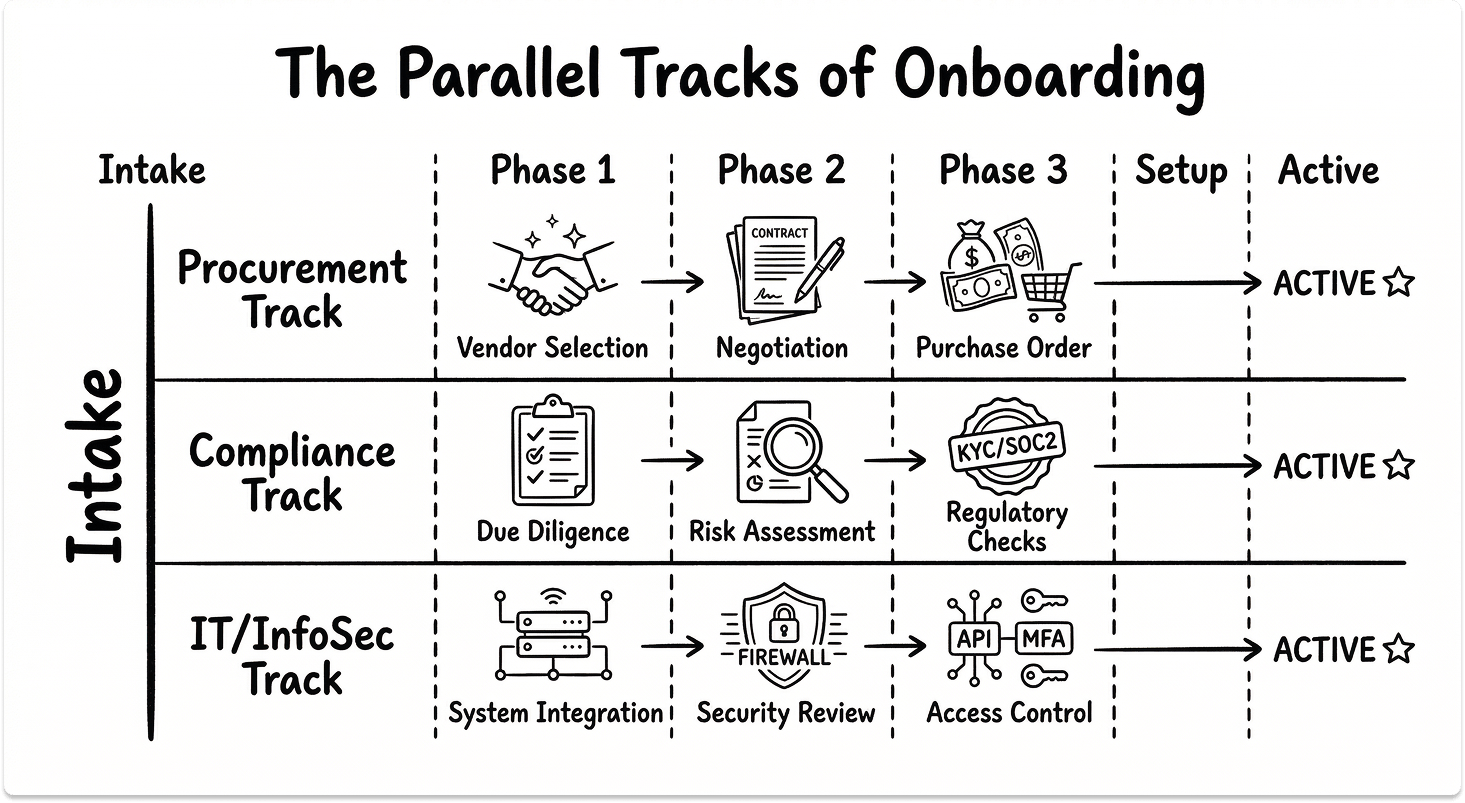
The procurement and compliance tracks are well-documented in most organizations. The IT track is not. It gets treated as a late-stage sign-off rather than a parallel workstream, and that is where the most expensive problems originate.
When IT joins the process after the contract is signed, security requirements become requests rather than obligations. When IT joins at intake, those requirements are negotiated into the agreement before either side has committed to anything.
The 5 Stages of the Vendor Onboarding Process
Stage 1: Vendor Intake and Pre-Qualification
Everything downstream depends on getting this stage right. Most onboarding failures do not originate in the compliance review or the contract negotiation. They originate here, because a vendor enters the process without the right information attached to it.
Start with a vendor onboarding form that captures the business justification, the requesting team, and specifically the systems or data the vendor will access. That last point is the one most intake forms leave out. Without knowing what the vendor touches, you cannot assign a risk tier, and without a risk tier, the depth of every subsequent review is guesswork.
Use a standardized vendor onboarding template for this form so every intake record contains the same fields and feeds into the same downstream review process.
Assign a risk tier before any review begins. The three-tier model maps directly to the scrutiny required:
- Tier 1 (Critical): vendor handles PII, PHI, or PCI data, or integrates with core infrastructure. Full review required.
- Tier 2 (Significant): vendor has system access or handles internal data. Targeted review required.
- Tier 3 (Standard): no sensitive data access, no core system integration. Basic check sufficient.

Run sanctions screening at intake, not later. Check OFAC, EU, and UN lists before the process moves forward. For Tier 1 vendors, run a preliminary financial health check here as well. A vendor that fails financial viability at intake saves you the cost of a full review.
If you are still in the process of deciding which vendor to onboard, see our guide to IT vendor selection criteria and checklist before proceeding to intake.
Typical timeline: 1-3 business days.
Common failure mode: skipping risk tier assignment because the team needs the vendor stood up quickly. The result is applying Tier 1 scrutiny to a Tier 3 SaaS tool, or worse, applying Tier 3 scrutiny to a Tier 1 data processor.
Stage 2: Documentation and Compliance Verification
Vendor onboarding compliance gaps are almost always documentation gaps. Segment your document requests by vendor type rather than applying one generic supplier onboarding checklist to every engagement:
SaaS and software vendors:
- W-9 or W-8BEN (tax classification)
- Certificate of Insurance (COI) with technology E&O coverage
- Master Service Agreement and Data Processing Agreement
- SOC 2 Type II report: read the audit period, scope boundary, and auditor exceptions, not just the cover page
- Penetration test summary from the last 12 months, conducted by an independent third party
- Subprocessor list with geographic locations
Infrastructure and hardware vendors:
- Business license and corporate structure documentation
- Last two years of audited financials or financial health summary
- Delivery SLAs and hardware replacement commitments
- Support escalation contacts and response time guarantees
Professional services and contractors:
- NDA and conflict of interest declaration
- Professional liability insurance confirmation
- Background check authorization
- Right-to-work documentation
Regulated industry additions:
- HIPAA: Business Associate Agreement (BAA) and PHI segmentation confirmation
- PCI DSS: scope letter confirming cardholder data isolation
- DORA: ICT third-party register entry and concentration risk assessment
- FedRAMP: authorization level confirmation for public sector workloads
More than 80% of organizations detect supplier risks only after onboarding begins, which means this stage is where most teams are already reacting rather than preventing. Running compliance checks before the contract is negotiated, not after, keeps your leverage intact.
Typical timeline: 3-7 business days for Tier 1, 1-3 days for Tier 2.
Common failure mode: accepting a SOC 2 certificate without checking the audit date or scope. A report completed 18 months ago against a narrower product version is not evidence of current security posture. Vendor onboarding compliance requires current documentation, not historical certification.
Stage 3: IT and Security Review
This is where IT vendor onboarding diverges most sharply from anything procurement owns. Every other stage has equivalents in standard supplier management frameworks. This one does not. It belongs to your team, and it needs structured ownership before the vendor is activated.
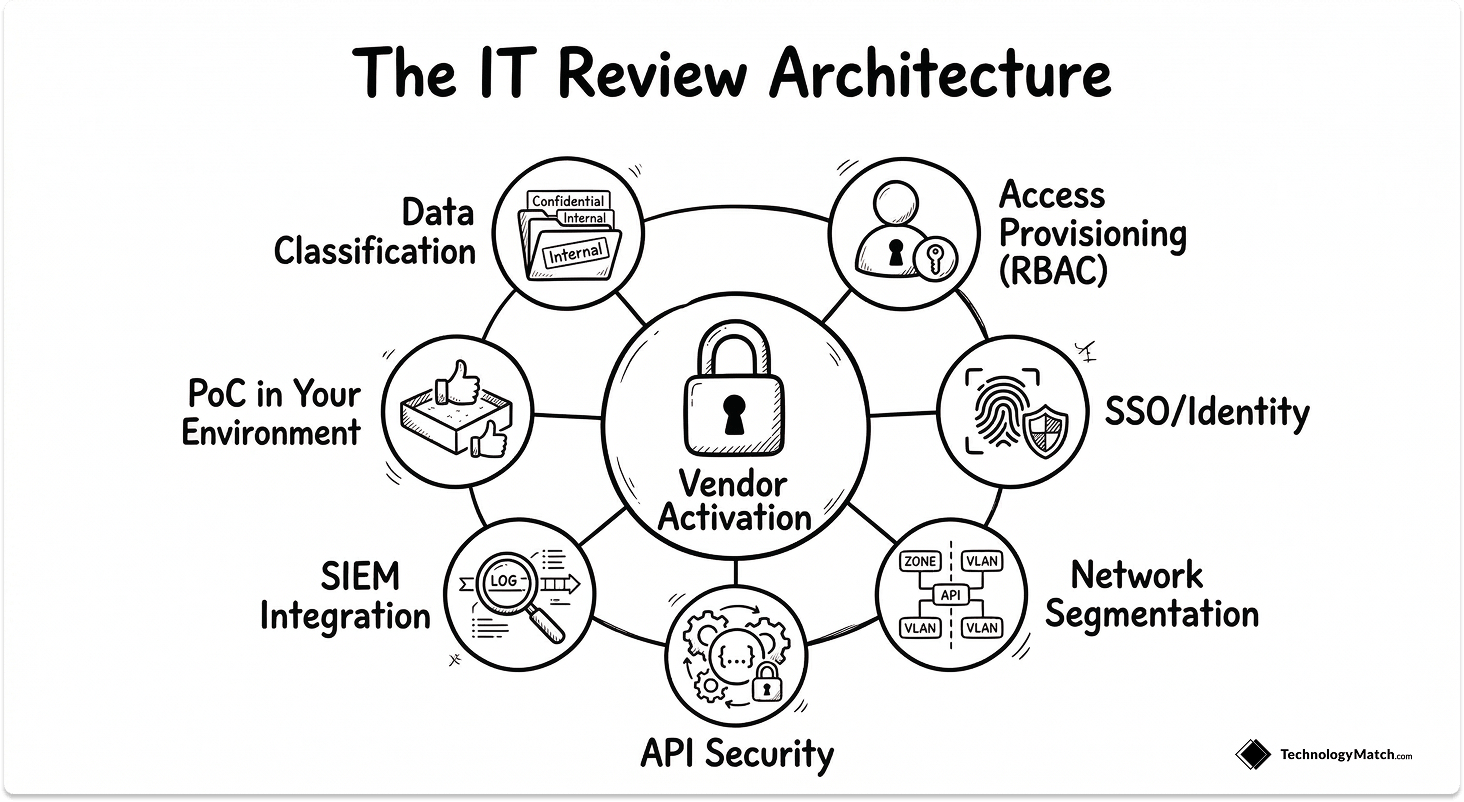
The IT and security review covers seven specific areas:
1. Data classification
Define what data the vendor will access, process, or store before any credentials are issued. Map it to your internal classification schema: confidential, restricted, or public. This single decision determines every access control that follows.
2. Access provisioning design
Define role-based access controls (RBAC) before any accounts are created. Apply the principle of least privilege at setup. Access controls retrofitted after activation are consistently weaker than those designed before it.
3. SSO and identity integration
Confirm SAML 2.0 or OIDC support. Configure SCIM provisioning for automated user lifecycle management. Enforce MFA at the identity provider level before the vendor accesses any system.
4. Network segmentation
If the vendor requires network access, define VLAN assignment, firewall rules, and ingress/egress controls before activation. Network access granted without segmentation creates lateral movement risk that persists for the entire life of the vendor relationship.
5. API and integration security
Issue API credentials with scoped permissions. Set rate limiting. Configure webhook signature validation. Confirm that all integration touchpoints produce audit logs in a format your team can read and export.
6. SIEM integration
Before the vendor is activated, confirm that their audit logs are exportable to your SIEM. Define the log format, retention period, and forwarding configuration. A vendor that cannot feed your SIEM is a blind spot from day one.
7. Proof of concept in your environment
Run the PoC in your own infrastructure, not the vendor's sandbox. Test the happy path, a failure scenario, and at least one integration edge case. Vendor-managed environments are pre-configured to perform well. Yours is not.
Typical timeline: 3-10 business days for Tier 1, depending on integration complexity.
Common failure mode: IT review scheduled after contract execution. At that point, you are configuring security around a commercial agreement rather than building security requirements into it.
Stage 4: Contract Finalization and Internal Approvals
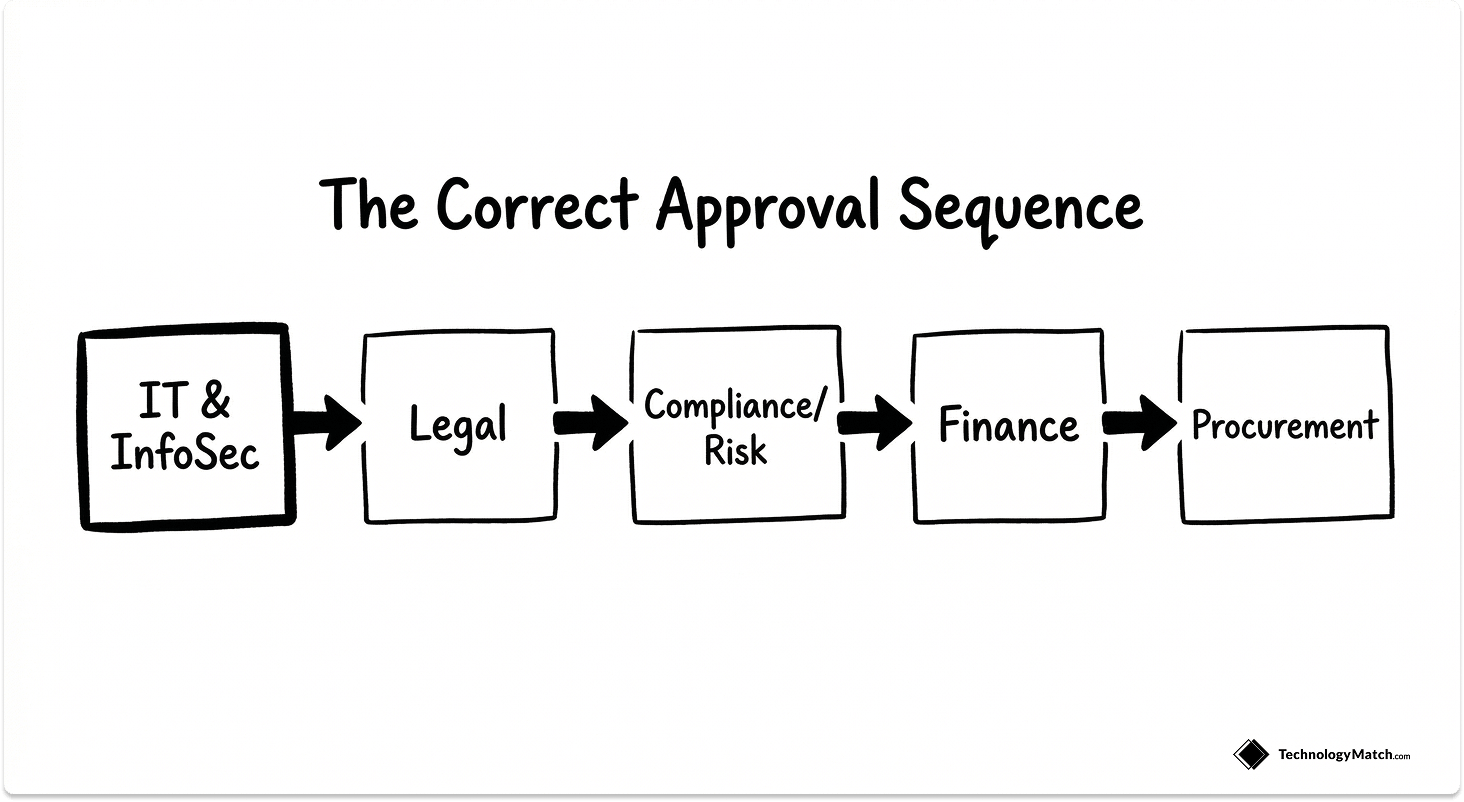
The approval routing stage carries more risk than most teams assign to it, because the sequence of approvals matters as much as the approvals themselves.
The correct sequence for Tier 1 vendors:
- IT/InfoSec signs off on the security exhibit and data processing terms
- Legal executes the MSA, DPA, liability caps, and termination clauses
- Compliance/Risk confirms regulatory alignment and records the vendor in the third-party register
- Finance validates banking details, sets up payment terms, and assigns budget codes
- Procurement confirms commercial terms and contract reference numbers
IT sign-off should come first, not last. When IT reviews a contract after legal has already executed it, any security requirements that were missed become change requests against a live agreement.
Key contract terms IT should verify before signing off:
- Data breach notification timeline: confirm it meets your regulatory obligations (72 hours under GDPR, for example)
- Audit rights clause: your right to request security documentation and conduct assessments throughout the relationship
- Subprocessor change notification: the vendor must notify you before adding new subprocessors that touch your data
- Termination and data deletion SLAs: how long data is held after contract end, and what the verified deletion process looks like
If this is the first time your team is formalizing this approval sequence, our guide on IT vendor management best practices covers how to structure the broader governance layer around it.
Typical timeline: 2-5 business days.
Common failure mode: IT approves system access before legal has executed the DPA, creating a window of data processing without a valid legal basis.
Stage 5: System Activation and Vendor Orientation
Activation is not the end of the new vendor onboarding process. It is the transition from setup to operational relationship. Treating it as a finish line is where most ongoing vendor risk originates.
When activating a vendor:
- Create the vendor record in your ERP or procurement system with the correct payment terms, contract reference, and contact hierarchy
- Grant system access according to the RBAC defined in Stage 3, not ad hoc and not based on the vendor's access request. Based on your defined scope.
- Confirm vendor portal access if applicable: document submission workflows, invoice routing, and the designated communication channel
- Deliver an orientation package covering the vendor's obligations. Include data handling requirements, breach notification procedures, escalation contacts, and the security behaviors you require them to maintain
- Schedule a 30-day check-in before the vendor relationship is considered stable. Confirm integration performance, resolve open access issues, and document the current state as your baseline
Typical timeline: 1-2 business days.
Common failure mode: vendor activated in payment systems before IT has confirmed access controls are live. This creates a window of unmonitored access that often persists for weeks before anyone notices.
The IT Vendor Onboarding Checklist
Use this vendor onboarding checklist for Tier 1 vendors end to end. For Tier 2, apply Stages 1-4. For Tier 3, Stages 1-2 are sufficient.
Vendor Onboarding Best Practices for IT Teams
Assign risk tier at intake, not after documentation is collected.
Tiering after the review begins means you have already invested effort at a depth that may not match the vendor's actual risk profile. The tier assignment is the first decision, not a conclusion drawn from the review.
Get IT into the process before the contract is signed.
I have seen more security gaps created by late IT involvement than by any other single factor. Once a contract is executed, every security requirement that was missed becomes a request to change a live commercial agreement. Vendors accommodate some of these. They ignore others.
Segment your supplier onboarding checklist by vendor type.
A SaaS tool and a cloud infrastructure provider both need onboarding. They do not need the same onboarding. Applying a single generic checklist creates unnecessary friction for low-risk vendors and misses critical documents for high-risk ones.
Set benchmark timelines per stage and measure against them.
The most common complaint about vendor onboarding is that it takes too long. Without per-stage baselines, that is an opinion. With them, it is a problem you can locate. A well-run Tier 1 onboarding process should complete in 12-20 business days end to end. Tier 2 should complete in 5-8 days. Tier 3 should complete in 1-3 days. If your process regularly exceeds these figures, the bottleneck is almost always in Stage 3 or Stage 4. Our breakdown of top IT vendor management challenges covers the structural reasons these bottlenecks form and how to address them.
Automate the repeatable. Keep judgment in human hands.
Document collection reminders, sanctions screening, certificate expiry alerts, approval routing, and RBAC provisioning are all automatable. Only 36% of organizations evaluate vendor security before sharing sensitive data, which suggests the bottleneck is process consistency, not process complexity. Automation enforces consistency. Risk assessment, contract review, and security architecture decisions require experienced judgment and should stay that way. For a look at the tools available to support this, see our guide to vendor management software for IT leaders.
Treat onboarding completion as the start of monitoring, not the end of the process.
The risk profile, access configuration, and compliance record you build during onboarding becomes the baseline for every reassessment that follows. 50% of organizations do not rank vendors by risk at all, which means they are managing their entire vendor portfolio at the same scrutiny level. The tiering framework you establish at onboarding determines how efficiently your team can monitor the relationship over time. For a detailed guide on when and how to reassess existing vendors, see our guide to IT vendor due diligence.
What Good Looks Like
A mature vendor onboarding process does not feel slow to the vendors going through it or to the teams managing it. It feels predictable. Vendors know what documents are needed and why. IT knows exactly what controls to configure and in what sequence. Legal and compliance review what they need to review, not what lands in their queue by accident.
The teams that run vendor onboarding best practices well share one trait: they defined what good looks like before the first vendor request arrived. They built the tiered checklist, assigned the owners, and set the timelines. The process runs at the speed of the preparation behind it.
Once a vendor is onboarded, the work shifts to monitoring. The risk profile, access configuration, and compliance documentation built during onboarding becomes the baseline that every subsequent review is measured against. Onboarding is not a gate you open. It is a foundation you build. For the governance framework that supports everything after activation, see our complete guide to vendor management.
Looking for IT Partners?
Tell us your requirements and we will find vendors that fit. If you're willing to move forward, we will prep them before your meeting so you conversation can start with context. This service is free to you.
FAQ
What is vendor onboarding?
Vendor onboarding is the structured process of qualifying, documenting, integrating, and activating a third-party supplier before they access your systems, data, or payment infrastructure. For IT teams, it covers three parallel workstreams: procurement (contracts, payment setup), compliance (documentation, risk assessment), and IT/InfoSec (access provisioning, integration testing, security configuration). The process spans 5 stages: intake and pre-qualification, documentation and compliance verification, IT and security review, contract finalization, and system activation.
How do organizations assess vendor compliance during onboarding?
Compliance assessment during vendor onboarding involves four layers. First, documentation collection and verification: SOC 2 Type II reports, ISO 27001 Statements of Applicability, penetration test summaries, and regulatory certifications are reviewed for current scope, not just validity. Second, sanctions and financial screening: OFAC, EU, and UN lists are checked at intake, with financial health assessed for Tier 1 vendors. Third, contractual alignment: DPA execution, audit rights clauses, breach notification timelines, and subprocessor change notification requirements are verified before sign-off. Fourth, security configuration review: the IT team validates that access controls, data classification, and monitoring configuration match the vendor's documented posture before activation.
How do you reduce vendor onboarding time without compromising compliance standards?
The answer is risk-based tiering applied at intake. The majority of onboarding time is consumed by applying Tier 1-level scrutiny to vendors that qualify as Tier 2 or Tier 3. Assign risk tier before documentation collection begins, then apply only the stages relevant to that tier. Tier 3 vendors should complete onboarding in 1-3 days. Tier 2 vendors in 5-8 days. Reserve the full 12-20 day process for Tier 1 vendors that genuinely require it. Automate document collection reminders, sanctions screening, and approval routing to eliminate coordination delays that inflate timelines without adding compliance value.