IT Vendor Management Frameworks: Models, Components & Implementation Guide
Build a strategic IT vendor management framework. This operational playbook details the 8 core components, risk tiering, and a 7-step implementation guide.

What Is an IT Vendor Management Framework?
An IT vendor management framework is a structured governance blueprint that controls the entire vendor lifecycle. It dictates exactly how your organization selects, monitors, and offboards third-party technology partners to minimize risk and maximize business value.
Why IT Vendor Management Frameworks Matter
Modern IT ecosystems run on dozens of interconnected vendors. You are no longer just buying standalone software. You manage a complex web of SaaS tools, cloud infrastructure providers, and specialized AI partners. Each of these entities carries its own dependencies and evolving compliance risks.
Without a centralized framework, your organization bleeds money. The average enterprise runs 250 or more SaaS applications and wastes $135,000 per year on unused licenses. Furthermore, 56 percent of that SaaS spend happens completely outside the visibility of the IT department.
The security implications are even more severe. According to Gartner, more than 60 percent of vendor-related disruptions originate from fourth-party dependencies. If your cloud provider uses a content delivery network, and that network experiences an outage, your operations halt. A strict vendor management framework enforces continuous SOC 2 and ISO compliance checks across this entire chain. It breaks down organizational silos and forces strict alignment between IT, Security, Legal, and Finance.
The 8 Core Components of an IT Vendor Management Framework
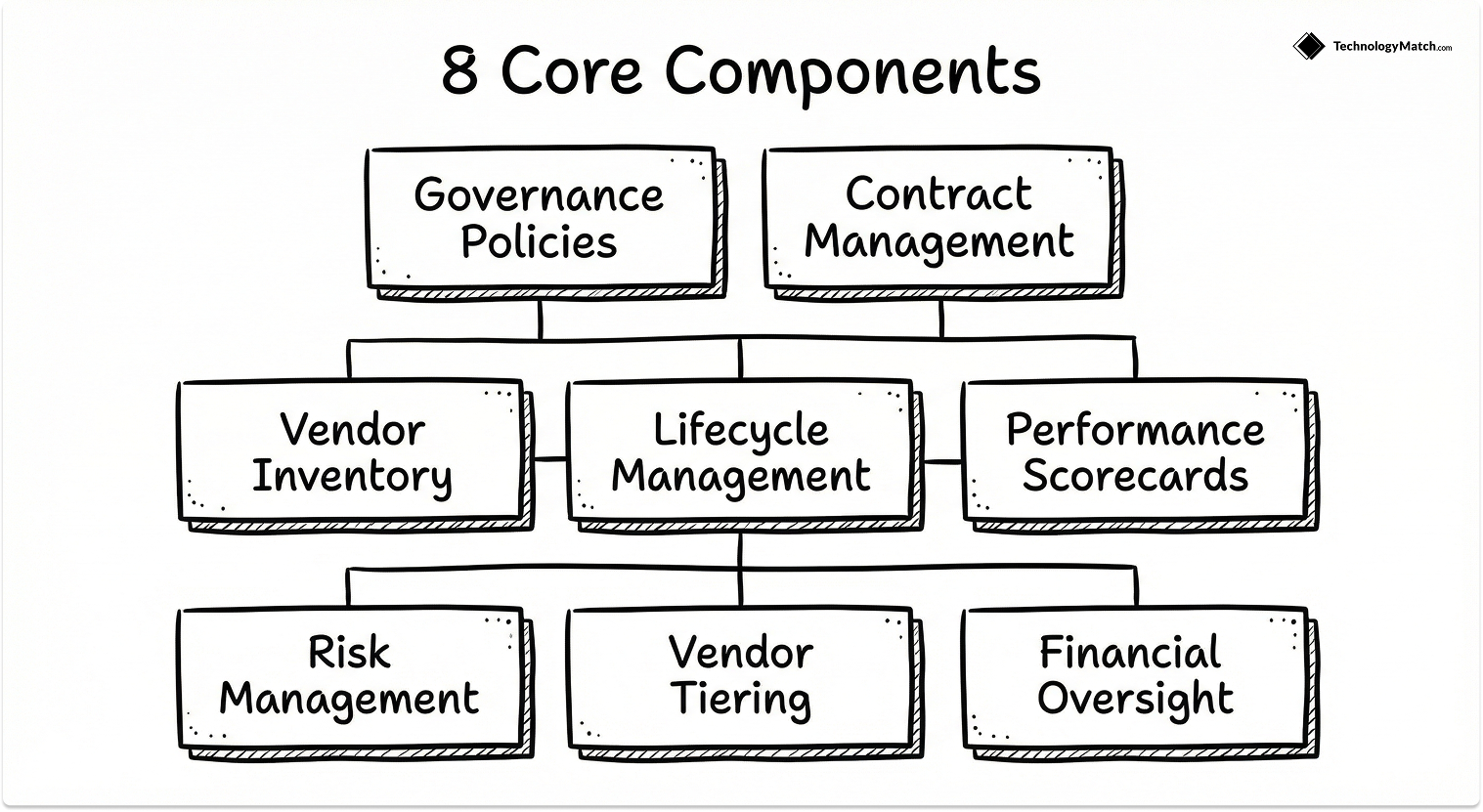
To build a secure technology supply chain, you need a defined architecture. I call this the Ecosystem Governance Model. It requires eight specific structural components to function correctly.
The Vendor Lifecycle Within a Framework
A framework operates on a continuous, repeating loop. I structure this using the Two-Ring Operational Model. The inner ring contains your governance enablers like policies, tools, and the roles defined in the table above. The outer ring represents the actual, sequential vendor lifecycle stages your team executes.

For a deep dive into executing these exact steps, refer to our complete guide to the IT vendor management process. Within the framework architecture, the lifecycle stages function as follows.
Discovery & Selection
You define precise business requirements and source potential vendors. You evaluate their technical capabilities against your existing enterprise architecture to ensure a seamless integration fit.
Risk Assessment & Due Diligence
You mandate comprehensive security questionnaires and compliance checks. You assess the financial stability and market position of the vendor to ensure they will not shut down or be acquired mid-contract.
Contracting & SLA Design
You negotiate pricing and lock in measurable performance targets. You define exact financial penalties for missed service levels and establish clear, non-negotiable data ownership rights.
Onboarding & Integration
You provision identity access management and connect the vendor to your systems via single sign-on and mature APIs. You configure role-based access controls and train your internal teams on the new technology.
Ongoing Monitoring & Performance Reviews
You track the vendor against the agreed-upon metrics. You hold quarterly business reviews to discuss raw performance data, address operational friction points, and review upcoming product roadmaps to ensure continued alignment.
Renewal, Transition, and Offboarding
You use hard utilization data to decide whether to renew the contract, renegotiate the terms, or replace the vendor. If replacing the vendor, you execute a strict exit plan to reclaim your data, verify deletion, and revoke all system access.
Comparing IT Vendor Management Framework Models

Not every organization needs the exact same level of administrative overhead. Copying an enterprise framework into a 50-person startup creates immediate operational bottlenecks. You must choose a framework model that matches your team size, agility requirements, and regulatory environment.
How to Build an IT Vendor Management Framework (Step-by-Step)
You cannot implement a mature governance architecture overnight. You must build your framework in structured phases to ensure adoption across your enterprise. I use a strict seven-phase deployment model to transition teams from reactive purchasing to proactive ecosystem orchestration.
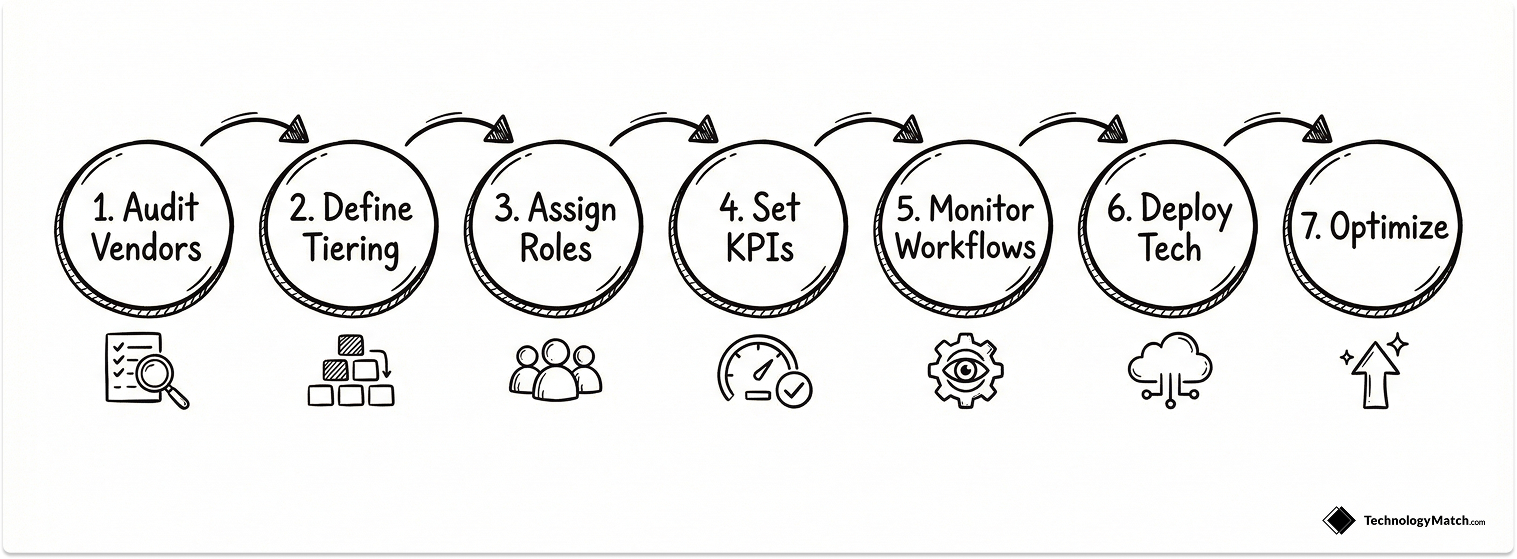
Phase 1: Audit your vendor landscape.
You must assess your current state before you write a single policy. Inventory all active vendors and map your existing procurement processes. Work with your finance department to identify hidden shadow IT spend. You cannot govern tools you do not know exist.
Phase 2: Define your vendor tiering model.
Treating all external partners equally wastes administrative resources. You must classify vendors by their operational criticality and risk profile. Allocate your management rigor based on this tiering system. High-risk strategic vendors require quarterly business reviews, while low-risk operational vendors require only automated monitoring.
Phase 3: Establish governance and assign roles (VMO, IT, Finance, Security).
Draft unified vendor policies that dictate onboarding criteria and security thresholds. Assign clear accountability by establishing a formal Vendor Management Office or a cross-functional governance committee. IT, Finance, and Security must know exactly who owns each stage of the vendor lifecycle.
Phase 4: Define KPIs and create performance scorecards.
You must hold vendors accountable to objective data. Define specific key performance indicators for each vendor tier. Track service level agreement adherence, delivery times, and actual business value realization. Build standardized performance scorecards to evaluate these metrics during your quarterly reviews.
Phase 5: Implement continuous monitoring workflows.
Set up regular review cadences to track metrics and hold operational check-ins. You must monitor vendor security postures and financial health continuously. A yearly static review leaves your organization exposed to new vulnerabilities.
Phase 6: Enable the framework with technology.
Manual spreadsheets break down when you manage more than fifty vendors. Implement a central vendor management platform to automate contracts, track metrics, and alert your team to upcoming renewals. Technology provides the single source of truth required for cross-departmental visibility.
Phase 7: Establish a quarterly optimization cycle.
Do not roll out the entire framework at once. Test your new policies with a small subset of vendors, collect feedback from your internal teams, and adjust your procedures. Schedule quarterly reviews of the framework itself to drive continuous improvement based on actual spend variance and compliance data.
Embedding Vendor Risk Management into the Framework
Vendor risk management is not a standalone process. It is an integral module operating within your broader framework. The framework governs the complete vendor lifecycle, while the risk management component handles the specific security assessments and continuous monitoring requirements.
You must execute comprehensive cyber, financial, and compliance risk assessments during the initial selection phase. Once the vendor is onboarded, you must deploy continuous monitoring tools to track vulnerability disclosures and map ongoing compliance against standards like SOC 2 and ISO 27001.
Common Blind Spots That Break Standard Frameworks
Many organizations build heavy frameworks that fail in execution. I track four specific blind spots that consistently ruin enterprise vendor management programs. Use this diagnostic checklist to identify gaps in your own architecture.

Integration Fit as a Primary Evaluation Metric
Most teams evaluate pricing and features but ignore integration compatibility. You must assess how well a vendor connects with your existing enterprise architecture. Evaluate their identity provisioning capabilities, single sign-on support, and overall API maturity. You should test these integrations in sandbox environments before you sign a binding contract. If you are evaluating technical tools, use resources like our CI/CD Decision Guide to understand necessary pipeline integrations.
Managing Vendor Ecosystems and Fourth-Party Risk
Your direct vendors are only part of your risk exposure. A data breach often originates from a sub-vendor you have never evaluated. According to Gartner, more than 60 percent of vendor-related disruptions come from these fourth-party dependencies. Ask your strategic vendors to map their dependencies and mandate notification clauses for any subcontractor changes.
The Human Layer and Cultural Alignment
Technical capability means nothing if the vendor is impossible to work with. You must assess collaboration readiness and communication styles during the evaluation phase. Include relationship metrics in your performance dashboards to measure team alignment and escalation maturity.
The Exit Strategy
Vendor exit is the highest-risk stage in the entire lifecycle, yet most teams ignore it. You must define an exit plan before signing any contract. Specify exact data export formats, migration timelines, and handover obligations. Maintain a strict offboarding checklist to verify data deletion and remove all system access.
Framework vs. Vendor Management Software
Terminology matters when building your strategy. The framework is your strategic blueprint and governance structure. The software is the tool you use to automate that blueprint.
Spreadsheets fail when your organization scales. When you manage a complex portfolio, you need a dedicated Vendor Management System to enforce your framework. These platforms centralize your contract metadata, automate your risk assessments, and alert your team 90 days before an auto-renewal triggers. Software operationalizes your governance.
The Vendor Management Framework for Lean IT Teams
Small IT teams assume frameworks are only for massive global enterprises. This is a dangerous misconception. A lean IT leadership team can punch well above its weight by adopting a simplified, tool-dependent framework model.
Lean teams must rely heavily on strict vendor tiering. You apply automated oversight tools to your operational vendors and reserve your manual, human-driven reviews strictly for your top five strategic partners. This approach minimizes administrative bloat while maintaining absolute control over your highest-risk technology investments.
Closing Thoughts: From Cost Center to Ecosystem Orchestrator
The era of ad-hoc software purchasing is over. IT leaders who view vendor management as a basic procurement task will continue to inherit unmanageable security risks and bloated contracts.
By implementing a formal IT vendor management framework, you stop treating vendors as external service providers and start treating them as components of your own enterprise architecture. You regain control of your data, optimize your technology budget, and transform your IT department from a reactive cost center into a strategic ecosystem orchestrator.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What are the components of an IT vendor management framework?
An IT vendor management framework requires eight core components. These include a centralized vendor inventory, a risk-based tiering model, governance policies, contract management workflows, performance scorecards, continuous risk management, financial oversight, and strict lifecycle management procedures.
How is a framework different from a vendor management process?
A vendor management process consists of the operational steps your team takes, such as negotiating a contract or onboarding a tool. The framework is the overarching governance architecture that defines the policies, roles, and accountability structures ensuring those processes are executed correctly and securely.
What KPIs should be included in a vendor framework?
You should track both technical outputs and business outcomes. Core KPIs include service level agreement compliance, mean time to resolution, adoption rates, cost per active user, security incident frequency, and the percentage of successful, on-time contract renewals.
How often should a vendor framework be reviewed?
You should review your overarching vendor management framework annually to align with new business goals and regulatory changes. However, you should evaluate the performance of your individual strategic vendors during quarterly business reviews.
What is the difference between vendor management and third-party risk management?
Vendor management covers the entire lifecycle of the vendor relationship, including sourcing, financial negotiation, and performance optimization. Third-party risk management is a specific discipline within that broader framework focused exclusively on identifying and mitigating security, compliance, and operational risks.